Botnets are known to be behind the biggest DDoS attacks of the past few years, from the Dyn attack in 2016 to the Mirai botnet-led attacks exploiting command injection vulnerability in 2023.
A botnet is the collection of malware-infected computers and networked devices (IoT, smart devices, etc.) that work together under the control of a single malicious actor or an attack group. Such a network is also known as a zombie army, and each infected device is called a bot/ zombie.
The number of bots in a botnet will vary across zombie networks, ranging anywhere between a few thousand to over a million compromised devices.
While the Hide ‘n Seek network has 24000 compromised devices, the Mirai bot network that widely disrupted internet usage in the US East Coast in 2016 is believed to have had 800,000 to 2.5 million infected devices.
Botnets are created by attackers to orchestrate a multitude of malicious activities like:
It is rather inexpensive and hassle-free to create botnets, especially where regulatory mechanisms and law enforcement are limited. So, it is a lucrative business model for developers and crime syndicates to offer attack-for-hire services.
Zombie armies are preferred by attackers because they are available as attack-for-hire services, which are inexpensive. Even a smaller botnet is extremely effective in causing massive damage. Given that the bots are globally dispersed, and no paper trails are left by them, the appeal in leveraging them to orchestrate attacks is unparalleled.
Devices (including computers, tablets, smartphones, smart TVs, soundbars, wireless CCTV, and other connected devices) are scanned using automation to identify common, unpatched, and insecure vulnerabilities, poor security misconfigurations, and hardcoded gaps.
Malware (Trojan horse virus or other malicious payloads) is attempted to be installed on the target devices through different means such as clickjacking, phishing, scams, password hacking, etc. The actual owner of the device may be unaware that their system is even part of such a nefarious network.
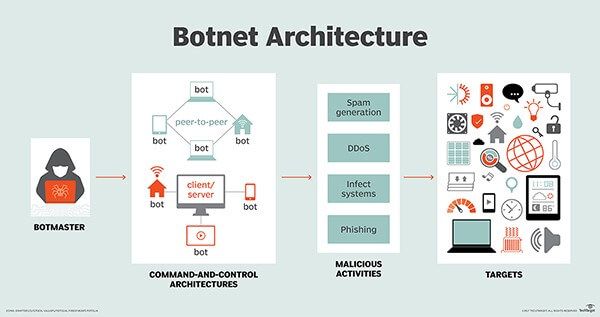
Once the desired number of bots are created, control of the bots is taken over by the attacker/ developer remotely using two command approaches:
The massive network of infected devices is then leveraged by attackers (directly or hired as a service) to fulfill their objectives.
Botnets come in various types, each tailored for specific malicious activities. Here are some common types of botnets:
DDoS Botnets: Distributed Denial of Service (DDoS) botnets aim to overwhelm a target’s online services by orchestrating massive traffic. This flood of requests surpasses the system’s capacity, leading to service disruptions and downtime. The impact includes financial losses, tarnished reputations, and troubles with normal business operations for the targeted entity.
Click Bots: Click bots engage in click fraud by generating fraudulent clicks on online advertisements. This deceptive tactic deceives advertisers into paying for non-authentic user interactions, leading to financial losses for advertisers and skewed metrics. The impact undermines the effectiveness of online advertising, reduces advertisers’ return on investment, and compromises the integrity of digital marketing ecosystems.
Scalper Bots: Scalper bots target online ticketing systems by rapidly purchasing large quantities of tickets, which are later resold at inflated prices on secondary markets. This practice limits access for genuine buyers, resulting in ticket scarcity, inflated consumer prices, and a contentious secondary ticket market.
Scraper Botnets: Scraper bots systematically extract data from websites, often for competitive intelligence, pricing information, or content duplication. The impact includes potential data theft, content plagiarism, and undermining the competitive advantage of targeted businesses.
Spam Botnets: Spam bots generate and disseminate a high volume of spam emails, contributing to the proliferation of unwanted and potentially harmful content. The impact overloads email systems, facilitates phishing attacks, and compromises the integrity of communication channels.
Zombies: Zombies encompass a network of compromised devices controlled by a central server. They are used for various malicious activities, including DDoS attacks, spam generation, and data theft. The impact enables versatile attacks and serves as a foundation for different botnets.
Backdoor Botnets: Backdoor botnets create a secret entry point (backdoor) on infected devices to provide remote access for future malicious activities. The impact facilitates persistent unauthorized access, data theft, or the deployment of additional malware.
P2P Botnets: P2P botnets operate as a peer-to-peer network where infected devices communicate directly, reducing dependency on a centralized command and control server. The impact increases resilience against takedowns, making detection and mitigation more challenging.
Understanding the nuanced characteristics of each botnet type is crucial for devising targeted cybersecurity strategies to combat specific threats associated with each variant.
Check out the 10 botnet detection and removal best practices to stay in control of your devices.
When devices are infected by malware and become part of the botnet, the impact could vary from increased Internet bills to loss of confidential data.
Additionally, the legal costs are high if one’s device is found to be part of a successful attack by the zombie network. It is important to ensure that devices are secured from becoming part of such a malicious network. Here are some ways:
Pre-emptively, businesses can beef up their security measures to mitigate zombie networks from attacking their networks/ applications with the help of managed DDoS service providers.
This post was last modified on February 13, 2024 13:11
File inclusion refers to including external files within a web application. These files can be… Read More
The Open Systems Interconnection (OSI) model is a conceptual framework for understanding and standardizing how… Read More
What is Gray Box Pen Testing? Gray box penetration testing is an application security testing… Read More