Most SaaS engineering teams use the CI/CD pipeline for software development.
Since a CI/CD approach enables faster, more collaborative, and more efficient development processes, leading to higher-quality software. No wonder that this is popular.
More frequent release cycles mean more opportunities for vulnerabilities to creep into the code.
While DevOps teams are central to running a CI/CD pipeline, since application security is gaining importance, more engineering teams are adding DevSecOps teams.
DevSecOps ensures that security is an essential part of the development cycle.
A big part of what they do is vulnerability scanning using code review and DAST tools. That said, patching these vulnerabilities is out of their hands as the vulnerability could exist in a third-party component or lack of developer availability.
A modern WAAP platform with virtual patching capabilities could be a great enabler in securing applications without any additional dependency on internal teams.
A Web Application and API Protection (WAAP) solution could play a critical role in the Continuous Integration/Continuous Deployment (CI/CD) process. It helps ensure security and protect applications and APIs from threats throughout the entire software development lifecycle.
Benefits of Integrating WAAP Platforms into the CI/CD Pipeline
Integrating a WAAP into the CI/CD pipeline offers several benefits, including:
1. Faster time to market
This is probably the biggest benefit, especially for SaaS companies that target highly regulated markets such as banking, healthcare, insurance, and so on. Integrating a WAAP platform into the CI/CD pipeline could automate most security testing and remediation.
2. Out-of-the-box coverage
Most WAAP solutions provide core rules that protect web applications and APIs against OWASP Top 10 vulnerabilities. So, even when applications have known vulnerabilities, such as cross-site scripting (XSS) or SQL injection (SQLi), the core rules provide some out-of-the-box protection.
3. Automated security testing
By including a WAAP like AppTrana in the CI/CD process, you can enable automated security testing for web and API applications. You could schedule daily or weekly scans and stay on top of vulnerabilities during sprints. AppTrana also has penetration testing as an add-on to help you uncover business logic vulnerabilities.
4. Virtual Patching
Once vulnerabilities are detected, understanding how many of them are protected by the core rules and how many can be protected by custom rules helps DevSecOps teams a great deal.
In our experience, 95% of vulnerabilities are protected using a combination of core and custom rules. This, in turn, helps the dev teams to prioritize patching those vulnerabilities that cannot be blocked at the WAF.
5. Anomaly detection
A WAAP platform like AppTrana monitors application and API traffic continuously during the entire deployment process. This provides visibility into potential security issues and allows for faster remediation in both staging and production environments.
6. Reduced downtime
Along with comprehensive coverage against OWASP Top 10 and zero-day threats, WAAP platforms protect against DDoS and Bot attacks. Therefore, a WAAP minimizes the risk of application and API downtime caused by security incidents, improving availability and user experience.
7. Improved compliance
Most compliance regulations, including PCI, mandate VAPT and WAF implementation. A WAAP solution like AppTrana that bundles DAST scanner and penetration testing along with an award-winning WAF also helps automate compliance checks for HIPAA, PCI-DSS, and GDPR.
8. Streamlined incident response
When WAAP is part of the CI/CD pipeline, it can automatically generate alerts and trigger remediation actions in response to detected threats, streamlining incident response and reducing the time required to address security incidents.
9. Secure coding practices
The integration of WAAP into the CI/CD process allows development teams to learn from detected vulnerabilities and security incidents continuously. This, in turn, helps them to improve coding practices over time and improve the security posture of applications and APIs.
Integrating a WAAP solution into the CI/CD pipeline is a best practice for ensuring comprehensive application and API security throughout the development lifecycle. It helps identify and mitigate security risks early in the process, improves compliance, and enables development teams to learn and enhance their application and API security measures continuously.
How to Integrate WAAP Platforms into CI/CD Pipeline
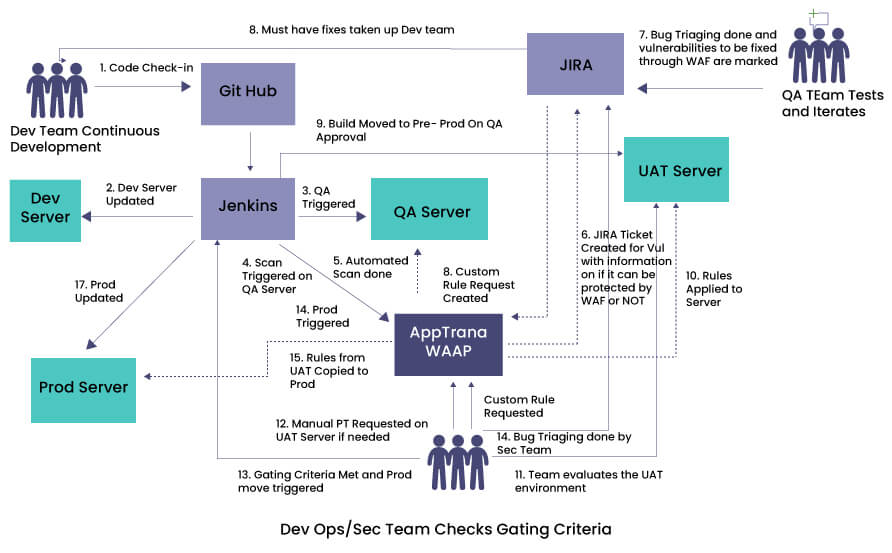
A high-level workflow demonstrates how WAAF could be integrated into SIEM, SOAR, Jenkins, and JIRA to automate security testing, patch management, and incident response.
- Dev team develops the code and initiates a check-in on GitHub
- Dev Server is updated by Jenkins on the check-in
- At a point, the build is moved to QA for testing. Jenkins pushes the build to the QA Server
- At this point, Jenkins triggers a WAAP platform like AppTrana to run an automated DAST scan on the QA Server
- AppTrana runs an infrastructure and application scan and creates the JIRA ticket for vulnerabilities with information on whether AppTrana can fix the vulnerabilities
- QA team does a triage
- Must-need fixes are pushed to developers for fixing on the code
- For other security vulnerabilities, the QA team can request virtual patches (custom rules) on WAAP through JIRA. (Steps 1 to 8 are repeated until QA gating criteria are met)
- Build is moved to UAT Server
- All rules, including custom rules, are applied on the UAT
- DevOps or security team evaluates the UAT environment
- If needed, manual penetration testing is requested on the UAT Server through JIRA
- Steps 5-8 are then repeated to meet the QA gating criteria
- Once the gating criteria are met, the trigger is given to update the production server
- Rules in the UAT server are copied to the prod
- Prod is updated
By following this approach, security is baked into the CI/CD pipeline to ensure that no known vulnerabilities can be exploited in the existing code.
Stay tuned for more relevant and interesting security articles. Follow Indusface on Facebook, Twitter, and LinkedIn.
