SQL injection has been the most common web vulnerability for three consecutive years. The 2025 Verizon DBIR reports it contributed to 12% of all data breaches, up from 9% the year before. In December 2024, a PostgreSQL SQL injection zero-day gave state-sponsored attackers a path into the US Treasury. In 2023, a single campaign used it to steal 2 million job seeker records across 65 websites in one month.
The fix has been known for two decades. The problem is applying it everywhere: legacy code, third-party plugins, AI-generated queries, features shipped under deadline. That gap is where attackers live.
This guide covers how SQL injection works, how to detect it early, and the seven techniques that close that gap.
30-Second Guide: How to Prevent and Stop SQL Injection
Prevention happens at the code level before an attack occurs. Stopping covers what you do when you are already vulnerable or under active attack. Here is where to start based on your situation.
| Situation | Action |
|---|---|
| Prevent: Building new features | Use parameterized queries ( no exceptions ) |
| Prevent: Legacy code you can’t rewrite yet | Add input validation at all entry points as interim cover |
| Prevent: Third-party plugin or vendor software | Virtual patch at the WAF edge, push vendor for a fix |
| Prevent: New developer on the team | Enforce prepared statements in code review before merge |
| Stop: Active attack in progress | Block at WAF, rotate database credentials, check logs for blast radius |
| Stop: Can’t identify where input enters the DB | Run a DAST scan to map all injection points immediately |
| Stop: Breach already occurred | Isolate affected endpoints, revoke DB permissions, run full vulnerability audit |
What are Databases and SQL?
A database is a collection of tables where data is stored and accessed. SQL, or Structured Query Language, communicates with and manipulates this data. SQL commands include “SELECT,” “UPDATE,” “INSERT,” “DELETE,” “CREATE,” and “DROP.”
Every time a user logs in, searches for a product, or submits a form, there is likely an SQL query running in the background.
What is SQL Injection?
SQL injection is a cyberattack technique where an attacker inserts malicious SQL code into an input field, manipulating the query the application sends to the database. Instead of the database processing legitimate user data, it executes attacker-supplied commands.
OWASP classifies SQL injection as a high-severity vulnerability in its Top 10 list, and it has been on that list for over 15 years. Despite being one of the most well-documented vulnerabilities in existence, it remains one of the most frequently exploited. The reason is simple: any application that passes unsanitized user input directly into an SQL query is vulnerable, and that mistake is easy to make.
What Causes SQL Injection?
SQL injection happens when an application fails to separate user-supplied data from the SQL query structure. The three most common causes are:
No input validation – The application accepts any value in an input field without checking whether it is the expected type, format, or length.
String concatenation in queries – Developers build SQL queries by directly embedding user input as a string, rather than using parameterized queries that treat input as data rather than executable code.
Verbose error messages – When a malformed query triggers a database error and that error is returned to the user, attackers learn the database type, schema structure, and query logic they need to refine their attack.
How does SQL Injection Work?
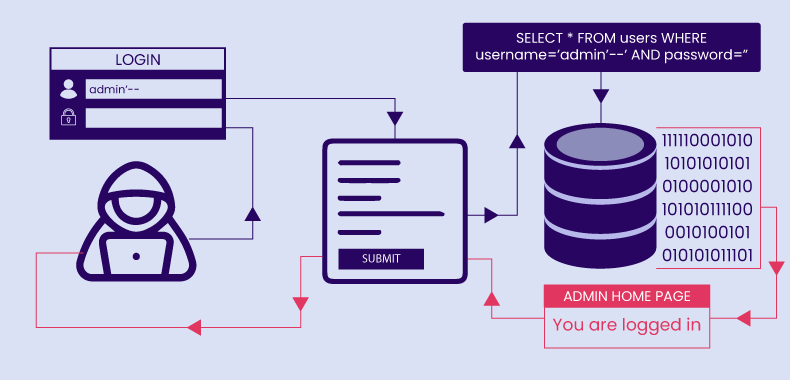
Here is a simple example of how SQL injection works:
A login form collects a username and password. The backend code looks like this:
$sql = "SELECT * FROM users WHERE username='$username' AND password='$password'";
An attacker enters the following as the username:
admin' --
The query becomes:
SELECT * FROM users WHERE username='admin'--' AND password=''
The double dash comments out the rest of the query. The password check is bypassed entirely, and the attacker logs in as admin.
This is the simplest form. Modern attacks are considerably more sophisticated, and AI tooling has made it far easier to test dozens of payload variations automatically in seconds.
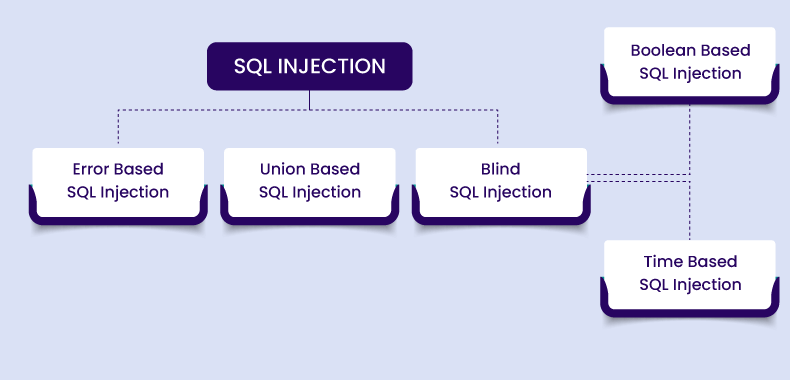
Types of SQL Injection Attacks
SQL injection attacks come in various types, each with its own characteristics. Here’s a rundown of the most common types of SQLi attacks:
- Error-Based SQL Injection
- Union-Based SQL Injection
- Blind SQL Injection
- Time-Based Blind SQL Injection
- Boolean-Based Blind SQL Injection
- Out of Band SQL Injection
1. Error-based SQL Injection
Error-based SQL injection involves sending malicious SQL queries to trigger errors or confirm vulnerabilities in the application. Attackers use these errors to gather information about the database structure or other sensitive details.
How to detect Error based SQL Injection?
Attackers may use SQL commands like single quotes, double quotes, or operators such as AND, OR, and NOT to provoke errors.
For example, entering http://demo.testfire.net/index.php?title=1′ might generate an error message like:
“You have an error in your SQL syntax; check the manual corresponding to your MySQL server version for the right syntax to use near ‘‘VALUE’’.
The error message gives him vital information like:
- DB used as MySQL
- Error in the syntax is a double quote
- The place of the error caused is at the end of the parameter
2. Union-based SQL Injection
In this type of SQL Injection, attackers try to exploit the vulnerability with the help of the “UNION” operator.
The UNION operator is used for combining 2 tables or performing 2 select queries simultaneously. In union operators, they remove duplicate rows or columns, which we try to execute simultaneously.
Union-based SQL Injection Example:
Suppose a web application builds an SQL query like this:
SELECT name, email, phone FROM users WHERE name = '[user_input]'
The user input is not properly sanitized, so an attacker could inject their own SQL code. For example, they could enter the following value as their name:
' UNION SELECT password, NULL, NULL FROM users --
This would result in the following SQL query being executed:
SELECT name, email, phone FROM users WHERE name = '' UNION SELECT password, NULL, NULL FROM users --'
The — at the end of the injected string is a comment symbol, which comments out the rest of the original query. So, the resulting query would be equivalent to:
SELECT name, email, phone FROM users WHERE name = ''
UNION SELECT password, NULL, NULL FROM users
This query would return a table with the user’s name, email, and phone number and a table with all the passwords in the user table. The attacker could then use this information to further compromise the system.
3. Blind SQL Injection
Blind SQL injection occurs when attackers cannot see the actual database content but infer information based on the application’s responses.
There are two main types of blind SQL injection attacks:
1. Boolean-based SQLi
2. Time-based SQLi
1. Boolean-based SQLi
In this type of SQL Injection attack, the attacker sends a series of SQL queries that evaluate either true or false, depending on whether the injected code was executed successfully.
The attacker can then use the application’s response to infer information about the database by constructing complex queries that probe for specific information.
Boolean-based SQLi Example: Deleting a user database using Boolean-based SQLi
How it works: A common online shop’s SQL database query could be like this:
SELECT ItemName, ItemDescription FROM Item WHERE ItemNumber = ItemNumber
So, a product URL on the online store could be
http://www.exampleshop.com/items/items.asp?itemid=999 or 1=1.
The SQL query could be
SELECT ItemName, ItemDescription FROM Items WHERE ItemNumber = 999 OR 1=1
One is always equal to one. It’s just a basic mathematical fact that holds true no matter where you are. SQL queries return all product names and descriptions in the database, even those you lack permission to access.
2. Time-based SQLi
This attack involves injecting a query that is designed to cause a delay in the application’s response. By measuring the time, it takes for the application to respond to the query, the attacker can determine whether the query was successful.
This technique is helpful when the attacker has no answer (error/output) from the application because the input validation has been sanitized.
Time-based SQL injection example
For example, let’s say there is a login form on a web application that uses a SQL query to check whether a user’s credentials are valid. The query might look something like this:
SELECT * FROM users WHERE username = 'admin' AND password = 'password123'
To perform a blind SQLi attack, an attacker could inject a query like this:
SELECT CASE WHEN (1=1) THEN pg_sleep(10) ELSE pg_sleep(0) END;
This query will cause the application to sleep for 10 seconds if the condition “1=1” is true. The attacker can determine whether the condition was true or false by measuring the time it takes for the application to respond to this query.
If the response takes 10 seconds, the attacker knows that the condition was true and that the application is vulnerable to blind SQLi. If the response is immediate, the attacker knows the condition was false.
Once the attacker has confirmed that blind SQLi is possible, they can start injecting more complex queries to extract sensitive information from the database.
To prevent blind SQL injection, ensure that all user inputs are properly sanitized and validated. Use parameterized queries or prepared statements to separate SQL logic from data, minimizing the risk of injection attacks. Additionally, implement robust error handling to avoid revealing sensitive information through error messages.
3. Out-of-Band SQL Injection (OOB SQLi)
Out-of-Band SQL Injection (OOB SQLi) is an advanced attack technique used when an application does not provide immediate feedback through error messages or direct responses. Instead of relying on traditional methods like error-based or union-based SQLi, attackers use external communication channels such as DNS or HTTP requests to exfiltrate data.
This technique is particularly effective when the database interaction is asynchronous or when restrictions prevent direct data retrieval. OOB SQLi is often leveraged in scenarios where blind SQL injection techniques fail due to security controls limiting on-screen output.
How Are SQL Injections Bot-Driven?
SQL injection attacks can be automated using bots, which can scale the attacks and make them more dangerous. Here’s how bots can drive SQL injection attacks:
- Automated Attack Execution: Bots can be programmed to automatically send SQL injection payloads to web applications. They can test various input fields and attempt different types of injections at high speeds, which would be difficult for a human to achieve manually.
- Scalability: Bots can execute thousands of SQL injection attempts simultaneously across multiple websites or applications. This scalability increases the likelihood of finding a vulnerability and makes it harder for organizations to defend against such attacks.
- Advanced Techniques: Bots can use advanced techniques to evade detection, such as rotating IP addresses, using proxies, and employing encryption. They can also employ sophisticated SQL payloads designed to bypass common security measures.
- Data Harvesting: Once a bot successfully injects malicious SQL code, it can automate the process of extracting sensitive data from the database. The data at risk may encompass usernames, passwords, credit card numbers, or other private information.
- Continuous Exploitation: Bots can continuously probe for vulnerabilities and exploit them over time. They can also adapt to changes in the application’s structure or security measures, making them persistent threats.
To combat bot-driven SQL injection attacks, implement rate limiting to control request volumes from single IPs and block malicious IPs. Additionally, use bot detection tools like CAPTCHA and behavioral analysis to identify and mitigate bot traffic.
Impacts of SQL Injection Attacks
SQL injection attacks can have extensive and damaging effects, varying based on the target. Key impacts include:
- Data Theft: Attackers can extract sensitive information such as usernames, passwords, credit card numbers, and personal details from a database.
- Data Modification or Deletion: Unauthorized manipulation or deletion of data can lead to significant data loss or damage, affecting the integrity and reliability of the information.
- System Takeover: By gaining administrative access, attackers can control systems, leading to further malicious activities like additional attacks, malware installation, or unauthorized changes.
- Financial Loss: The costs of SQL injection attacks can be substantial, including direct expenses for system restoration and data recovery, as well as indirect losses from disrupted business operations and lost revenue.
- Regulatory and Legal Consequences: Businesses may face financial penalties or legal action due to data breaches, particularly those handling sensitive information, such as financial institutions or healthcare providers.
- Reputation Damage: A successful attack can severely damage a company’s reputation, leading to long-term harm to future growth and profitability.
- Operational Disruption: Downtime caused by attacks can result in lost revenue and customer frustration, further impacting the business’s reputation.
Additionally, attackers often combine SQL injection with other tactics like insufficient authentication, DNS hijacking, XSS, and DDoS attacks, which can exacerbate the financial damage and lead to more severe system compromises.
Most Notorious SQLi Attacks in History
The following incidents represent some of the most consequential SQL injection breaches from recent attacks to cases that shaped how the industry thinks about database security.
BeyondTrust / US Treasury breach (December 2024 — February 2025)
This is the most significant confirmed SQL injection incident in recent memory. Chinese state-sponsored attackers, tracked as Silk Typhoon, breached BeyondTrust’s Remote Support SaaS platform in December 2024, compromising at least 17 enterprise customer instances including the US Treasury Department. Rapid7 researchers investigating the breach discovered that the attack chain relied on a PostgreSQL zero-day, CVE-2025-1094, which allowed SQL injection through improper handling of invalid UTF-8 characters in psql, PostgreSQL’s interactive terminal. The SQL injection enabled arbitrary code execution, which was then chained with a BeyondTrust-specific vulnerability to achieve full system compromise. The Treasury breach exposed unclassified documents related to sanctions and foreign investment reviews. PostgreSQL patched CVE-2025-1094 on February 13, 2025. This incident is a clear demonstration that SQL injection vulnerabilities exist not just in application code but in the database infrastructure itself and that state-level attackers actively hunt for them.
ResumeLooters campaign (November–December 2023, disclosed February 2024)
Between November and December 2023, a threat group tracked as ResumeLooters compromised at least 65 job listing and retail websites, primarily across the Asia-Pacific region, using SQL injection attacks. The campaign stole over 2 million records including names, email addresses, phone numbers, employment history, and date of birth data from job seekers. The stolen data was sold on Chinese-speaking Telegram channels. The group used widely available penetration testing tools including sqlmap and Metasploit, underlining that high-volume SQL injection campaigns do not require sophisticated custom tooling, just unpatched input validation.
Kotak Life Insurance / MOVEit (2023)
Attackers exploited a SQL injection zero-day in Progress Software’s MOVEit Transfer application (CVE-2023-34362). The breach cascaded across hundreds of organizations globally. Confirmed victims included Maximus, whose breach compromised 11.3 million patient records, along with the BBC, British Airways, and multiple UK and US government agencies. It remains one of the most wide-reaching SQL injection-driven breaches on record.
WooCommerce unauthenticated SQL injection (2021)
In July 2021, WooCommerce disclosed a critical SQL injection vulnerability affecting its core plugin and several associated plugins. The flaw allowed unauthenticated attackers to extract data from any affected store’s database without needing login credentials, impacting millions of WordPress-based eCommerce sites.
Kaseya ransomware campaign (2021)
The REvil group exploited SQL injection vulnerabilities in Kaseya VSA servers to gain remote access and deploy ransomware. The attack cascaded across over 1,500 businesses managed by Kaseya’s MSP customers.
Drupal SQL injection (2014)
Drupal disclosed a critical SQL injection vulnerability in core versions 7.0 through 7.31. Lack of input sanitization was the root cause. The vulnerability was so widely exploited that Drupal’s security team issued an unusual public warning stating that any site not patched within seven hours of the announcement should be considered compromised.
Target data breach (2013)
The Target Corporation breach exposed the payment card data of 40 million customers. SQL injection played a role in the initial database access phase of the attack chain.
SQL Injection and AI-Powered Applications: New Attack Surfaces
AI-powered applications introduce new SQL injection risks that traditional guidance does not fully address.
Natural language query interfaces – Applications that translate user natural language input into SQL queries (text-to-SQL) create a new injection vector. If a user’s natural language input influences the generated SQL without sanitization, an attacker can craft inputs designed to produce malicious queries. Parameterized execution of AI-generated SQL is essential.
AI agents with database access – LLM-based agents that have direct database read/write access via tools introduce the risk of prompt injection leading to SQL injection. An attacker who can influence the prompt the agent receives can potentially instruct it to execute destructive SQL commands. Defense requires sandboxing agent database permissions to the absolute minimum and validating all SQL the agent generates before execution.
AI-generated code vulnerabilities – Code generation tools (Copilot, Cursor, etc.) sometimes produce SQL queries using string concatenation rather than parameterized queries, particularly for simpler queries where the risk is less obvious. Security teams need to include SQLi pattern scanning in their code review process for AI-generated code, not just human-written code.
RAG pipelines with user-controlled queries – Retrieval-augmented generation systems that query a database based on user input inherit the same injection risks as any other database-connected application. The fact that the query is being generated by an LLM does not make it safe.
How to Detect SQL Injection Attempts
SQL Injection detection is the first line of active defense. The following signals appear in application logs and monitoring systems before a successful exploit.
1. Unusual SQL characters in input parameters
Single quotes, double quotes, semicolons, comment sequences (– or #), and SQL operators in input fields that normally expect simple values. An attacker testing a login form with admin' OR '1'='1 is the classic example.
2. Database error messages in responses
A spike in database errors tied to specific endpoints indicates someone is experimenting with malformed queries. Well-configured applications should never surface raw database errors to users.
3. High request volumes targeting specific endpoints
Automated scanning tools send large numbers of requests to input-accepting endpoints in a short window. Login forms, search fields, product filters, and API query parameters are the most common targets.
4. Suspicious authentication bypass patterns
Authentication endpoints are among the most actively probed targets in SQL injection campaigns. Attackers inject logical conditions into login fields that force the query to always return true, bypassing password validation entirely. The most common payloads include ' OR '1'='1, ' OR 1=1 --, and admin'--, where the double dash comments out the password check completely. More sophisticated attempts arrive encoded such as URL-encoded (%27 OR %271%27%3D%271), hex-encoded, or with SQL comments inserted mid-keyword (OR/**/1=1), specifically to slip past WAF rules that block the plain-text version. Repeated login failures from the same IP or across distributed IPs containing any of these patterns in credential fields should be treated as active injection probing, not routine failed logins.
5. Application and web server log anomalies
Encoded payloads (hex, URL encoding, base64 in unexpected positions), repeated parameter tampering, and requests with unusual query structures are visible in logs before any successful exploitation occurs. Regular log analysis and SIEM alerts on these patterns catch probing attempts early.
For a deeper breakdown of real-world patterns and payloads that appear in application logs, see our guide on SQL Injection in Logs: What to Look For.
How to Prevent SQL Injection Attacks?
To effectively prevent SQL injection attacks, securing all inputs and server-side processes is essential. While client-side validation helps, it is not sufficient against determined attackers. Here is a comprehensive approach to prevent and mitigate SQL injection attacks, featuring 7 key mitigation techniques:
1. Parameterized queries (prepared statements)
This is the most effective individual defense. Parameterized queries separate the SQL command structure from the user-supplied data. The database treats the input as a value, never as executable code.
cursor.execute("SELECT * FROM users WHERE username = ? AND password = ?", (username, password))
Java example (JDBC):
PreparedStatement stmt = conn.prepareStatement("SELECT * FROM users WHERE id = ?"); stmt.setInt(1, userId);
This should be the default for every database interaction in every language. There is no practical downside to using parameterized queries.
2. Input validation and sanitization
Validate that input matches the expected type, length, format, and range before it reaches any database interaction. An integer field should only accept integers. An email field should only accept valid email formats. Reject anything that does not match.
Sanitization removes or encodes characters that have special meaning in SQL. These two steps together significantly reduce the attack surface, even before the query layer.
PHP example using filter_var:
$username = filter_var($_POST['username'], FILTER_SANITIZE_STRING);
Validation is a first filter, not a complete defense on its own. Combine it with parameterized queries.
3. Escaping for user input
When parameterized queries are not feasible (legacy codebases, specific database drivers), use the database-specific escape function to neutralize special characters.
PHP/MySQL example:
$user_input = mysqli_real_escape_string($connection, $_POST['user_input']);
Always use the escape function that matches the specific database.
mysqli_real_escape_string for MySQL, pg_escape_string for PostgreSQL. Never roll your own escaping logic.
4. Stored procedures (with parameterization)
Stored procedures encapsulate SQL logic in the database. When properly parameterized, they prevent direct injection because user input is passed as parameters, not embedded in the query string.
Correct SQL Server example:
CREATE PROCEDURE GetUser @username NVARCHAR(50)
AS BEGIN
SELECT * FROM users WHERE username = @username;
END
The common mistake is concatenating parameters inside the procedure instead of using parameterized logic. That recreates the vulnerability inside the procedure. Always parameterize within the stored procedure itself.
5. Least privilege database accounts
The application’s database user should have only the permissions it needs for normal operation. A web application that only reads product listings should not have DELETE or DROP permissions.
MySQL example:
GRANT SELECT ON database.products TO 'webapp'@'localhost';
If an attacker successfully injects a query, least-privilege limits the blast radius. They cannot drop tables, read sensitive tables outside the application’s scope, or write data if the account lacks those permissions.
6. Continuous scanning and penetration testing
No static defense is sufficient in isolation. Regular DAST (Dynamic Application Security Testing) scans identify injection vulnerabilities in running applications, including those introduced by code changes that were not security-reviewed.
AppTrana’s embedded DAST scanner runs continuous inspection and is backed by a manual penetration testing team that verifies findings and reduces false positives. This matters because automated scanners can produce noise. A managed service that combines automation with expert review gives security teams actionable results.
7. Web Application Firewall (WAF) with AI-powered detection
A WAF sits between the internet and the application, inspecting all incoming traffic before it reaches the application layer. It blocks SQL injection attempts matching known patterns, but modern WAFs do more than pattern matching.
Rule-based example:
SecRule ARGS "(select|union|insert|delete|drop)" "deny,log"
This blocks basic payloads. But signature-only WAFs are increasingly bypassed by encoded, fragmented, or AI-generated payloads that avoid known patterns.
AppTrana WAAP combines signature-based rules with machine learning and behavioral analysis. It builds a baseline of normal request behavior for each application and flags anomalies, including zero-day injection techniques that have no existing signature. When a new vulnerability is discovered and a code fix is not immediately deployable, the WAF provides virtual patching, applying a protection rule at the edge without touching the application code.
SQL Injection Protection: How WAF Fits Into Your Defense Stack
SQL injection protection is not a single tool or a single practice. It is a stack.
The innermost layer is the code itself: parameterized queries, input validation, and stored procedures. These prevent injection at the source. They are the strongest defense and should be non-negotiable for all new development.
The middle layer is access control: least-privilege database accounts, proper error handling (never exposing raw database errors), and database activity monitoring.
The outer layer is the WAF. It catches attacks that reach the application despite the inner layers, provides virtual patching for legacy code and third-party applications you cannot directly modify, and gives visibility into attack patterns targeting your specific endpoints.
AI-powered WAFs like AppTrana WAAP add behavioral intelligence to this outer layer. They catch novel payloads, adapt to evasion techniques, and reduce the manual tuning burden on security teams. AppTrana’s zero false positive guarantee means that blocking rules do not fire on legitimate traffic, which is the operational failure mode that causes teams to switch WAFs to monitor-only mode and lose their protection entirely.
Prevent SQL Injection with AppTrana WAAP
AppTrana WAAP provides the outer layer of SQL injection protection that code-level defenses cannot cover alone.
It inspects all HTTP traffic in real time, blocking injection payloads before they reach the application. The detection engine combines rule-based matching with machine learning and behavioral analysis, catching both known payload patterns and novel attack techniques that bypass signature-only systems.
AppTrana’s managed security team reviews and validates protection rules before deployment, ensuring that blocking is accurate and does not affect legitimate traffic. Virtual patching allows teams to apply targeted protection for known vulnerabilities in third-party applications or legacy code without waiting for a code fix.
You can start by determining if your website has SQL Injection risks with AppTrana Free Trial.
Watch how AppTrana detects and blocks SQL injection
Stay tuned for more relevant and interesting security articles. Follow Indusface on Facebook, Twitter, and LinkedIn.