Hacks and data leaks have affected many major players in recent years, including AT&T Vendor(9 Million accounts), T-Mobile (37 Million accounts), JD Sports(10 Million), MyDeal (2.2Million), Dropbox (nearly 69 million accounts), Flagstar bank (1.5 Million) and eBay (145 million).
Those were bad. But not the worst. What are the most notorious hacks in history? They’re subject to debate, but these 39 attacks categorized under OWASP Top 10 would be strong candidates for the title.
Broken Access Control
1.British Library Cyberattack (2023)
In October 2023, the British Library suffered a major cyberattack by the Rhysida ransomware group, leading to the exposure of 600GB of sensitive data after a failed ransom demand. Attackers likely exploited weak authentication measures, including compromised third-party credentials and the lack of multi-factor authentication (MFA) for contractors, allowing unauthorized access.
The breach severely disrupted operations, taking months to restore critical services and costing the library an estimated £6–7 million. This incident underscores the importance of strong access controls, MFA enforcement, and regular security audits to prevent unauthorized access.
2. MGM Resort Breach(2023)
MGM Resorts International suffered a breach orchestrated by the hacking group Scattered Spider, leading to a system outage for the $14 billion gaming giant. Researchers have connected ALPHV/Blackcat/Scattered Spider ransomware groups to attacks on MGM, with ALPHV/Blackcat openly claiming responsibility.
The group, boasting persistency in the network with super administrator privileges, deployed ransomware after locking out MGM’s network, indicating extensive visibility and implanted backdoors. Scattered Spider claimed to have exfiltrated data, threatening to expose any PII found unless a significant ransom was paid.
Explore the risks of data exfiltration and how to prevent such breaches
3. First American Financial Corp Data Leak (2019)
The US-based mortgage settlement and real estate financial services company First American Financial Corp faced one of the biggest hacks in history in 2019. Ben Shoval, a real estate developer, had found that approximately 885 million files containing sensitive customer data from 2003 onwards were freely available. He notified the company about the same.
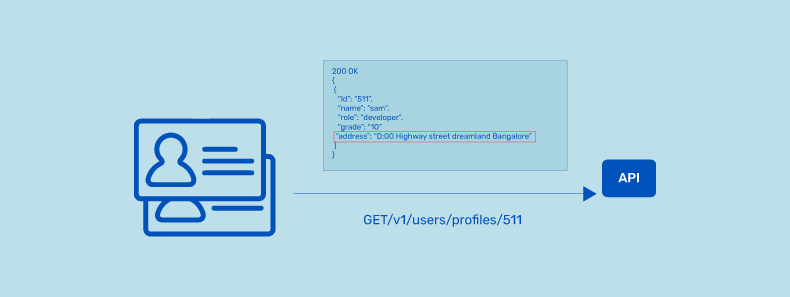
This leak was a result of a human error. In January of that year, the internal team discovered an Insecure Direct Object Reference (IDOR) flaw during a manual pen test. This bug allowed users to access private information using a specific URL and sequentially changing its numbers. And without proper authentication, any user could access any information freely.
4. Quora Data Breach (2018)
100 million (50% of the user base) of Quora users’ data were exposed in one of the biggest hacker attacks in 2018. This occurred because malicious third parties gained unauthorized access to its internal systems.
The breach was discovered on November 30, 2018, and Quora publicly announced the incident on December 3, 2018.
Quora officials have acknowledged the discovery of unauthorized access, and their CEO, Adam D’Angelo, has declared that they have determined the root cause and implemented corrective actions.
According to Quora, the information that was compromised included:
- Account information, such as usernames and email addresses
- Encrypted passwords
- Data imported from linked networks, such as Facebook and Twitter
Quora said it had taken immediate action to investigate the incident and notified law enforcement authorities. The company also said that it had reset the passwords of affected users and had logged them out of their accounts.
The Quora data breach highlights the importance of strong password hygiene and the need for users to use unique passwords for each online account. It also underscores the need for companies to implement robust security measures to protect their users’ personal information.
5. Cambridge Analytica Scandal (2018)
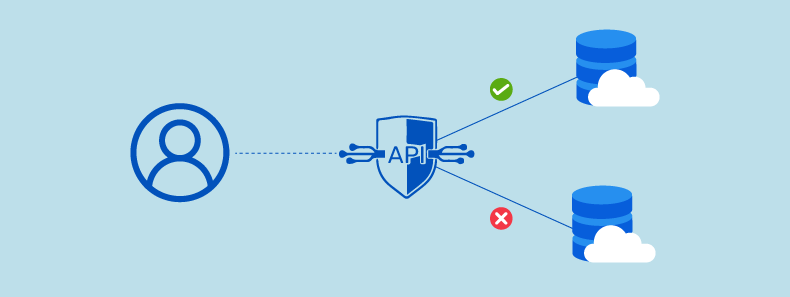
In 2018 it was discovered that political consulting firm Cambridge Analytica had obtained access to the personal information of millions of Facebook users without their consent. This was made possible by a broken access control vulnerability in Facebook’s application programming interface (API) that allowed third-party developers to access user data.
The scandal brought to light the issue of data privacy and the need for stricter access control measures to protect user data. Facebook faced widespread criticism for its role in the breach and was fined $5 billion by the U.S. Federal Trade Commission for violating users’ privacy.
6. Marriott International (2018)
One of the largest hacks in history was the Marriott International data breach in 2018 that exposed 500 million guest records, including passport details, credit cards, arrival-departure dates, PII, etc.
As companies strengthen their systems after major breaches like this, many are also investing in retail media to improve how they reach customers. Here is a useful guide on retail media that explains platforms, formats, and how brands use it to drive performance.
Attackers accessed Marriott’s guest data through email spoofing to spread malware into the vulnerable guest reservation system using legacy I.T. infrastructure. Britain’s Information Commissioner’s Office (ICO) fined the company 18.4 million pounds for GDPR violations.
Marriott discovered they had been hacked after a security tool flagged an unusual database query. Despite the query with administrator privileges, an investigation showed that the assigned account owner did not make it, indicating that someone else had taken control of the account.
7. The University of California, Los Angeles (UCLA) Data Breach (2014)
In 2014, UCLA suffered a data breach that exposed the personal information of approximately 4.5 million individuals. The breach was caused by a vulnerability in a database that allowed the attacker to gain unauthorized access to sensitive data.
The data compromised in the breach included names, Social Security numbers, dates of birth, addresses, and medical information of patients and staff associated with the university’s health system.
8. Target Data Breach (2013)
Target suffered a data breach that exposed the credit and debit card information of approximately 40 million customers. The breach was caused by a misconfigured network segment allowing the attacker to access Target’s payment system.
The security misconfiguration that allowed the breach to occur was related to the access controls and security protocols used in Target’s payment processing system. The system was designed to segregate the network traffic of different departments and systems within Target, but this segregation was not properly implemented. As a result, the hackers could access the payment processing system through a vendor portal that had access to the system but was not properly secured.
The significant date breach at Target was a result of multiple factors, such as the absence of adequate system protection, making them susceptible to phishing attacks. In addition, prior warnings were not taken seriously.
Access Control Defence
- Implement Least Privilege Access
- Enforce Multi-Factor Authentication (MFA)
- Use Role-Based Access Control (RBAC)
- Conduct regular access audits
Cryptographic Failures / Sensitive Data Exposure
9. Snowflake Breach (2024)
In May 2024, the financially motivated threat actor UNC5537 launched a large-scale data breach targeting Snowflake customers, exploiting exposed legitimate credentials rather than sophisticated hacking techniques. Threat actors obtained stolen login details—either purchased or found online—and accessed accounts lacking multi-factor authentication (MFA).
This allowed them to infiltrate cloud storage systems, steal sensitive data, and extort victims for financial gain. The hack, one of the largest in 2024, led to the sale of data from Ticketmaster and Santander on cybercrime forums, highlighting the critical need for strong credential management and MFA enforcement to prevent such attacks.
10. Twitter Breach (2022)
The Twitter APIs faced a classic case of excessive data exposure in 2022 when attackers sold 5.4 Million users’ information on a hacking forum. In January 2023, attackers further scraped 400 Million users’ public and private data, selling it on the dark web.
The excessive data exposure flaw enabled the attacker to check whether email ids and phone numbers were linked to Twitter accounts. This data breach left several users, including high-profile users like celebrities, politicians, and activists, exposed to social engineering, targeted phishing attacks, and identity thefts, among others.
11. Exactis (2018)
The Exactis data breach of 2018 is yet another biggest hack in history. Exactis is a marketing and data aggregation company that stores customer data across various variables to target ads.
It had stored nearly 2TB of customer data on a publicly accessible cloud server. This left data of 340 million customers, including 400 variables of personal characteristics, exposed to the public.
12. Facebook Data Breach (2019)
The social media giant Facebook faced a massive data breach in 2019 that exposed over 533 Million Facebook users’ data. Sensitive personal information such as location, phone numbers, user IDs, account names, etc., were stolen and posted in hacking forums. The exposed data was scraped from two datasets from third-party Facebook apps.
The data breach occurred because Facebook was storing user passwords in plain text, meaning the passwords were not encrypted. This made it easy for hackers to access user accounts by guessing or cracking passwords.
13. The Yahoo Hacks (2013 & 2014)
Poor Yahoo. At one time, the king of search engines, it’s fallen on hard times lately. People are abandoning it in droves for the likes of Google, Bing, and others. Its cause wasn’t helped much when in 2016, it revealed major hacks that had occurred years before.
Over one billion (yes, billion) Yahoo accounts were compromised in 2013, including names, DOBs, security questions, contact details, and passwords.
A further 500 million accounts were hacked in 2014. How many accounts overlap with the first hack is unknown, so the number of affected accounts is unclear. But it’s a lot.
It’s the largest hack of a single entity in the history of the internet. That’s not a great claim to fame for a company trying to woo users back to its flock.
And although Yahoo is much less relevant than it used to be, the tendency of people to reuse passwords and security questions has serious implications. If you had a Yahoo email account in 2009 but switched to Gmail with the same password, the hack means someone could access your current email account.
Reports indicate that the encryption used to protect the data was outdated and could be broken with ease.
Data Protection Measures
- Encrypt all sensitive data at rest and in transit
- Use strong encryption algorithms (AES-256, TLS 1.3)
- Securely manage encryption keys
- Avoid weak hashing algorithms for password storage
Injection Attacks
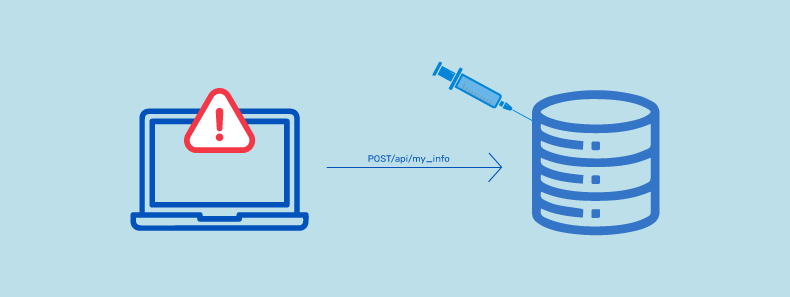
Injection attacks aren’t just a thing of the past—they’re evolving. While SQLi and XSS have compromised millions of records, prompt injection is the latest security risk targeting AI-powered systems.
14. ResumeLooters Attack(2023)
In late 2023, a threat actor known as ResumeLooters executed a series of cyberattacks, compromising over 65 recruitment and retail websites. They employed SQL injection and Cross-Site Scripting (XSS) techniques to infiltrate these sites, resulting in the theft of more than two million email addresses and other personal information. This incident underscores the persistent threat posed by injection attacks and highlights the necessity for robust security measures to protect sensitive user data.
15. Cl0p Gang Exploits Zero-Day in MOVEit Transfer App (2023)
In a significant cyberattack, the Cl0p hacking group targeted Progress Software’s MOVEit Transfer app with a zero-day SQL injection vulnerability on May 27. Over 1,000 organizations and 60 million individuals worldwide were impacted, including high-profile victims like British Airways and the BBC.
Progress Software addressed the issue (CVE-2023-34362) on May 31, but reports of data breaches continued. CISA flagged the vulnerability, emphasizing the potential for extensive corporate data exposure and future extortion threats.
Explore the AppTrana’s threat coverage for Moveit Transfer SQL vulnerabilities.
16. Asia Pacific Websites Hit by GambleForce (2023)
A cybersecurity company called Group-IB has identified a new threat actor named GambleForce. This group has been active since September 2023. It has targeted over 20 websites related to gambling, government, retail, and travel websites in Australia, China, India, Indonesia, the Philippines, South Korea, Thailand, and Brazil.
GambleForce uses basic but effective techniques like SQL injections and exploiting vulnerable website systems to steal vital information, including user credentials. Check out the detailed blog on how to stop SQL injection attacks.
Between September and December 2023, they successfully attacked 24 organizations in 8 different countries, compromising six websites in Australia (travel), Indonesia (travel and retail), the Philippines (government), and South Korea (gambling).
17. Kaseya Ransomware Attack (2021)
Kaseya is an IT solutions provider for MSP and enterprise clients. The company was a victim of a ransomware attack during the American Independence Day weekend in 2021. The REvil group, known for their ransomware attacks, claimed responsibility for this attack, impacting over 1500 of Kaseya’s clients.
Attackers exploited unpatched SQL vulnerabilities in the company’s VSA servers to carry out this attack. This may not be the biggest attack in terms of size, but it has been a notorious hack in the recent past.
18. WooCommerce Leak (2021)
WooCommerce offers a popular ecommerce plugin for WordPress CMS. In 2021, it was found that several of its plugins, features, and software versions were vulnerable to SQLi, and several attacks occurred as a result. Unpatched flaws in the plugin exposed data on 5 million websites to theft.
19. The Heartland Payment Systems Hack (2008)
The credit card payment processor is one of the world’s largest, processing about 100 Million monthly transactions for Visa, Mastercard, American Express, and Discover.
Its system was compromised in 2008, and an estimated 130 Million customer accounts were accessed, making it one of the largest credit card hacks in history.
An SQL injection attack targeted Heartlands’ computer. The attack manipulated the code of a web script, granting the attackers access to a web login page.
Albert Gonzalez and two Russian hackers placed sniffer programs within the Heartland system. These sniffers intercepted credit card credentials in real time and relayed the data back to them.
The sniffers remained undetected for six months. The attack went unnoticed for several months as it traversed Heartlands’ system, enabling the attackers to obtain enough data to produce physical credit cards with the information coded into the magnetic strip.
20. Equifax Data Breach (2017)
One of the biggest hacks in history is the Equifax data breach that happened in 2017. Equifax, a credit reporting agency, had several security lapses that enabled attackers to access sensitive PII, date of birth, social security numbers, address, driver’s license numbers, etc., of over 143 million customers.
Attackers were able to wreak havoc for 76 days before they were discovered. The company spent USD 1.4 billion in recovery after this data breach.
Equifax used Apache Struts as a web framework, like many Fortune 100 companies, to build its APIs and applications. An XXE vulnerability in the company’s customer complaints web portal made the initial hack possible. The vulnerability in the framework was left unpatched by Equifax’s internal failures.
The attackers made their way through the portal into other servers owing to a lack of proper segmentation. And a flaw in the company’s API enabled attackers to access data and credentials without authenticating themselves.
The attackers encrypted and exfiltrated data to escape detection for months. The non-renewal of an encryption certificate for one of the internal security tools made this possible. It was not until 2019 that the certificate was renewed.
Injection Prevention Strategies
- Use prepared statements & parameterized queries
- Implement strict input validation & sanitization
- Apply least privilege access for databases
- Deploy Web Application Firewalls (WAFs)
Security Misconfigurations
21. Microsoft Teams Outage (2023)
On June 28, 2023, a significant Microsoft Teams outage occurred due to increased traffic identified by Microsoft in early June. Worldwide users were affected from 10:49 AM to 12:55 PM UTC.
The outage primarily impacted web access and new desktop client sign-ins, while existing and mobile clients remained unaffected. The root cause was an authentication error in a Teams back-end service responsible for configuration settings, causing operational failures.
Regrettably, the service was mistakenly set to require authentication, causing denied configuration requests and operational failures, hindering user access via specified channels.
Secure Configuration Practices
- Disable unnecessary features and default admin accounts
- Use secure default settings
- Regularly audit & update security configurations
Vulnerable and Outdated Components
22. T-Mobile API Breach (2023)
On Jan 19, 2023, T-Mobile revealed a security breach affecting around 37 million customers, with unauthorized access to a vulnerable API lasting over six weeks. The breach, starting on November 25th, 2022, exposed names, emails, phone numbers, and birthdates.
With data such as account lines and service plans compromised, prepaid and subscription customers were specifically impacted. The incident underscores the importance of robust API discovery to prevent unauthorized access in a distributed ecosystem.
23. Colonial Pipeline Ransomware Attack (2021)
Colonial Pipeline is an American fuel company that supplies fuel to a large section of the east coast of the US. During the Mother’s Day weekend, attackers unleashed the DarkSide ransomware on the company’s IT systems, taking advantage of the upcoming holiday.
This ransomware brought the entire IT systems of the company to a grinding halt and led to the suspension of pipeline operations for a week. The attackers targeted the billing infrastructure while the existing pumping systems worked fine.
However, the services could not be continued without being able to bill customers. The halting of the operations caused a fuel shortage along the east coast which caused panic buying among retail consumers and rescheduling flights among airline consumers.
Attackers had stolen 100GB of data in this recent major hack in history and demanded a ransom of 75 bitcoins in exchange for the decryption tool. The company had to oblige and pay the ransom to resume operations.
One of the main factors was a lack of proper security controls and protocols within Colonial Pipeline’s IT systems. The hackers could exploit a vulnerability in a legacy VPN (Virtual Private Network) system that had not been properly patched or updated. This vulnerability allowed the attackers to access Colonial Pipeline’s network and deploy the ransomware.
A lack of preparedness and response planning by the Colonial Pipeline also facilitated the attack. The company was initially slow to respond to the attack and struggled to contain the damage and restore operations. This led to significant disruption to the fuel supply chain in the southeastern United States and caused shortages and price increases at gas pumps.
24. JBS Ransomware Attack (2021)
In another holiday cyberattack, global meat supplier JBS was hit by a massive attack during the 2021 Memorial Day weekend. This was one of the biggest hacks in history to affect a player in food production. Attackers managed to get into JBS networks using flaws in the system and threatened to delete files or cause disruption until a cryptocurrency ransom was paid.
This ransomware attack brought its beef and pork slaughterhouses in North America and Australia to a standstill. The company obliged the attackers’ demand and paid USD 11 million ransom to resume its operations.
25. Strava API Breach (2018)
Another major hack in history that exposed global heatmaps of military bases was the Strava API breach in 2018. Strava is a fitness app widely leveraged by military personnel to track their fitness and training routines.
The poorly designed API vulnerabilities exposed the 3 trillion data points, including 1 billion online activities. The attackers were able to collect worldwide user activities from January 2015 to September 2017.
Patch and Update Strategies
- Keep all software & dependencies updated
- Apply patches immediately for critical vulnerabilities.
- Monitor security advisories for critical patches
Identification and Authentication Failures
26. Identification and Authentication Failures (2024)
A ransomware attack on UnitedHealth Group compromised the personal data of over 100 million individuals. The breach occurred when attackers used stolen credentials to access a Citrix portal that lacked multi-factor authentication (MFA), allowing them to enter the system using only basic login details.
After gaining access, the hackers demanded a financial ransom of $22 million in Bitcoin, which United Healthcare paid. The attack exposed sensitive health insurance details, medical records, billing information, and personal identification numbers, highlighting the critical need for robust authentication measures.
27. Sharp HealthCare Cyberattack (2023)
Sharp HealthCare, San Diego’s most significant health provider, announced that it has begun notifying 62,777 patients that some of their personal information was compromised during a hacking attack on the computers that run its website, sharp.com.
The investigation confirmed that an unauthorized third party successfully breached the web server, powering the sharp.com website briefly on January 12. During that time, the third party downloaded a patient data file.
28. Okta’s Customer Data Support Breach (2023)
Okta reported a security breach, initially affecting 366 customers between January 16 and January 21. The incident led to a $2 billion market cap loss. The breach involved unauthorized access to files in Okta’s customer support system for 134 customers from September 28 to October 17, 2023.
An attacker, compromising an Okta employee, accessed a service account via stored credentials in the employee’s personal Google account, allowing manipulation of customer support cases. Okta later revised the impact, stating that only two customers had their legitimate sessions hijacked using session tokens during the incident.
29. Norton LifeLock Stuffing Attack (2022)
Norton LifeLock warns of a security breach affecting 925,000 customers in a credential-stuffing attack. Personal details like names, phone numbers, and addresses may be exposed, and there’s a potential compromise of Norton Password Manager vaults.
Starting on December 1, 2022, the breach saw a surge in failed login attempts by December 12, 2022. Gen Digital, Norton LifeLock’s parent company, secured all affected accounts by December 22. The attack exploited the common practice of password reuse across multiple accounts, affecting nearly a million active and inactive Norton LifeLock accounts.
Credential stuffing involves exploiting authentication and session management vulnerabilities, precisely what the “Broken Authentication” category addresses.
30. LinkedIn API Breach (2021)
One of history’s most recent and biggest hacks is the LinkedIn API breach of 2021. Personal records of over 700 million users – 92% of the user base – were scraped from the platform and put up for sale in a hacker forum. Why did this happen? Attackers found a public API without authentication and breached it to scrape content.
Since users’ personal and professional information on this platform was exposed, an advisory was issued to users that the risk of identity theft, targeted phishing attacks, and impersonations are high. Users were advised to remain vigilant.
31. The iCloud Celebrity Hacks (2014)
Accounts – including many A-list celebrities like Jennifer Lawrence and Kate Upton – were accessed on the Apple cloud storage platform in 2014.
Hackers used a combination of brute-force guessing and phishing schemes to gain entry. They sent official-looking emails to account owners with instructions to log in and change their security credentials—Anyone who did so gave the hackers everything they needed to get in and copy files.
Several (seemingly) unconnected individuals were investigated over the next few months. At least two were found guilty and sentenced to between 9-18 months in late 2016 and early 2017 for crimes related to the hack.
Authentication Security Measures
- Enforce strong password policies
- Implement Multi-Factor Authentication (MFA)
- Ensure secure session management
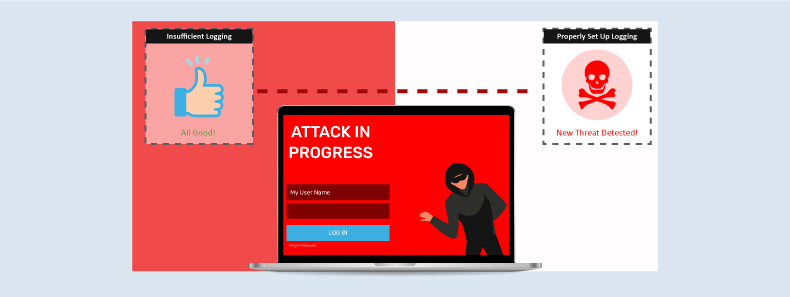
Security Logging and Monitoring Failures
32. SolarWinds Supply Chain Attack (2020)
SolarWinds is a network-monitoring software that nuclear labs leverage, intelligence agencies, several Fortune 500 companies, and the Pentagon. The company faced a supply chain attack in 2020 that exposed over 50 million records.
Russian hackers compromised and gained access to SolarWinds’ production environment and introduced malicious code into Orion, a network monitoring product. They sent out a tainted software update which more than 18000 customers installed.
The update installed Trojan horses into client systems and created a backdoor called SUNBURST. Breaking the chain of trust, this supply chain attack wreaked havoc on an undisclosed number of individuals and companies in the software supply chain.
The attackers gained access to SolarWinds’ systems through a combination of tactics, including password guessing, spear-phishing, and exploiting a zero-day vulnerability in the Orion software.
The attackers were able to evade detection for several months by exploiting insufficient logging and monitoring practices.
Effective Logging & Monitoring
- Enable detailed security logging
- Use SIEM solutions for real-time monitoring
- Implement automated alerts for suspicious activity
Server Side Request Forgery (SSRF)
33. Microsoft Exchange Server Vulnerability (2021)
In early 2021, Microsoft Exchange, an email and collaboration system used by many organizations, was targeted by a sophisticated hacking campaign. The attack was attributed to a state-sponsored group based in China.
Microsoft has reported that attackers use all four zero-day vulnerabilities to target organizations running Exchange Server products. One of the flaws, CVE-2021-26855, is a server-side request forgery (SSRF) vulnerability that enables the server to run commands that it should not have been allowed to execute.
The attackers have also used CVE-2021-26857 to run code under the system account on the Exchange server.
The remaining two zero-day flaws, CVE-2021-26858 and CVE-2021-27065, allow the attacker to write files to any part of the server. The attackers have deployed web shells on the compromised server to steal data and perform further malicious actions.
The scope of the attack was significant, with tens of thousands of organizations reportedly affected worldwide. Microsoft issued emergency patches for the affected Exchange servers, but many organizations were slow to apply them, leaving their systems vulnerable to attack.
The attack was highly sophisticated and well-coordinated, and it is believed to have been carried out to steal sensitive data for espionage purposes.
34. Capital One Breach (2019)
The Capital One breach of 2019 exposed customers’ sensitive personal, banking, and financial information, including Canadian social insurance and US social security numbers, loan applications, credit scores, credit limits, account balances, etc. This hack affected 100 million US and 6 million Canadian consumers, making it a major recent breach in history.
The attacker, a former software engineer at Amazon Web Services (AWS), orchestrated this attack and stole 80,000 bank account numbers and 140,000 US social security numbers, apart from exposing sensitive information.
While working at the company, she built a tool to scan misconfigured AWS accounts. Using the tool, she could hack into and access more accounts, including those belonging to Capital One. The breach was made possible due to misconfigured firewalls used by Capital One.
The company was fined USD 80 million by the US Office of the Comptroller of the Currency (OCC) owing to the breach and paid USD 190 million in settling customer lawsuits.
The former AWS employee was arrested and charged with the data breach that involved using a server-side request forgery (SSRF) attack against the AWS infrastructure that stored Capital One’s data.
SSRF Defence Tactics
- Restrict outbound network access
- Validate & sanitize user-supplied URLs
- Use allowlists for permitted requests
Lack of Resources & Rate Limiting
35. Bandwidth.com(2021)
A DDoS attack targeted Bandwidth.com, causing a major disruption to their services and portals and resulted in a widespread outage of voice services for their customers. The incident also highlighted how cloud-based business communication platforms, including VoIP phone services and CPaaS providers, remain vulnerable to upstream infrastructure attacks and service disruptions.
Although the issue was resolved, the incident highlighted the significant cost of such attacks in terms of financial losses and customer dissatisfaction.
The attack is estimated to have reduced the company’s CPaaS revenue by $9 million to $12 million for FY’21, with a $0.7 million impact in the third quarter. Indirect costs, such as damage to the company’s reputation and missed opportunities, also add to the overall impact.
36. GitHub (2018 and 2015)
This is the biggest known DDoS attack of all times wherein the source-code management/web hosting platform was flooded with a massive influx of traffic at the rate of 1.3TBps (the highest-ever recorded), sending packets at a rate of 126.9 million per second.
The attack was orchestrated using the mem caching method (a database caching system to improve website speed) instead of botnets to spoof GitHub’s IP address and amplify the requests sent to the platform.
The attack lasted 10 minutes and the platform was unavailable for 5 minutes. The attack could be stopped within this timeframe only because the platform had DDoS protection in place. However, recovery took nearly 1 week.
GitHub also faced a politically motivated DDoS attack in 2015 wherein browsers of everyone visiting Baidu (a popular web search platform in China) were infected with JavaScript Code, creating a botnet. The infected systems sent voluminous HTTP requests to the platform, causing downtimes across the GitHub network.
37. Dyn (2016)
Dyn, a major DNS provider, faced the second-largest DDoS attack. It directly disrupted the services of 80 of its clients (causing crashes and downtimes) including corporate heavyweights like Amazon, Netflix, Airbnb, Twitter, PayPal, Reddit, Spotify, Fox News, HBO, New York Times, Visa, etc.
It was orchestrated using a massive botnet of 100,000 IoT devices (created by infecting vulnerable devices with malware called Mirai) to overwhelm the Dyn platform with traffic spikes at the rate of 1.2TBps, lasting nearly 1 day. As a result of this attack, the company lost 14,500 domains and faced a total cost of USD 110 million.
38. BBC (2015)
One of the world’s largest news broadcasters, BBC, faced a series of DDoS attacks by the anti-Islamic State (IS) group, New World Hacking.
The attack brought the BBC’s on-demand TV service, iPlayer services, and radio services to a halt for nearly 3 hours with the significant disruption that lasted the entire day. The attack was orchestrated by leveraging 2 AWS-based DDoS tools to harness unlimited bandwidth and sent requests at the rate of 600 Gbps.
39. SpamHaus (2013)
A leading spam-filtering organization that helped filter 80% of all spam, SpamHaus, was faced with a highly damaging DDoS attack in 2013.
The attackers orchestrated a DNS reflection attack at the rate of 140-300 Gbps and lasted for a week nearly, heavily impacting their email servers, website, DNS IPs, and offline services.
To learn more about how rate limiting can help mitigate DDoS attacks like these, check out our detailed blog on Rate Limiting Strategies
Resource & Rate Limiting Strategies
- Implement rate limiting & request throttling
- Use timeouts & API quotas
- Monitor & log traffic spikes
- Leverage DDoS protection Software
Don’t become another statistic.
The dreaded hack. It can happen to anyone, anywhere, anytime. When will the next “most notorious hacks” happen? Probably sooner than you think.
Phishing schemes. DDoS attacks. Brute-force attacks.
Don’t make an appearance in the next edition of hacker history. Be smart. Be proactive. Be safe and secure.
While reflecting on past attacks, catch up on 2025’s latest cybersecurity stats here!
Stay tuned for more relevant and interesting security updates. Follow Indusface on Facebook, Twitter, and LinkedIn