IT systems usually save in a database user’s personal information such as passwords, credit card numbers, house address, telephone number, id number, etc. When the system is not protected effectively from unauthorized access there is a high probability that a hacker might exploit that vulnerability and steal that information. That vulnerability is ‘Sensitive Data Exposure’.
Apart from precious data loss, sensitive data loss has a much more serious impact on ‘brand image’ and reputation. As per a leading E-commerce CEO, ‘Sensitive Data Exposure has become a real nightmare to all of us! It may cause a real embarrassment if such incidents occur to us.’
How Is Data Exposed?
Here are 2 online ways, your data can be exposed:
- Intrusion: Intruders can gain access to your data through a weakness in web applications. Attackers may steal or modify such weakly protected data to conduct credit card fraud, identity theft, or other crimes. In September, Vodafone 2013 notified two million customers their personal and financial information had been breached. Generally, Organisations don’t publicly disclose breaches of internal information and trade secrets, as they are with regulated consumer data. Additionally, there’s no fraud algorithm to alert victims about illicit use of such data, leaving many cases of espionage undiscovered. Most of what we know publicly about this genre of the threat comes from incident responders, intelligence analysts, and malware researchers who compile and share their knowledge with the community.
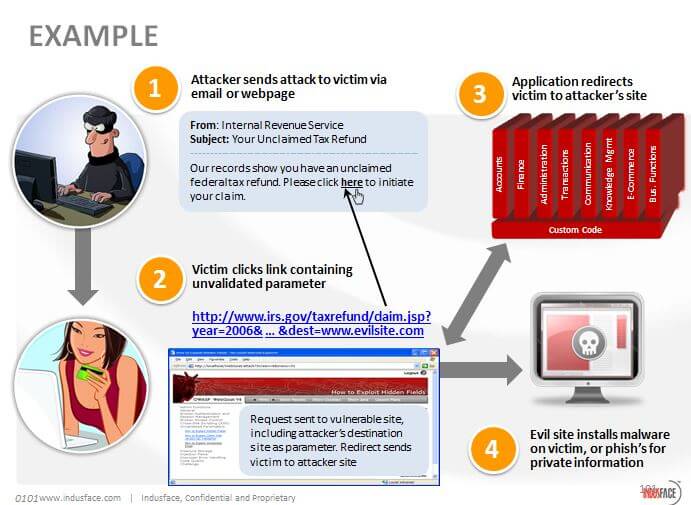
- Phishing: This is an attack on customers rather than on organizations. This is a clever method of extracting information from unsuspecting individuals. An e-mail, designed to look like it originated from a reputable company, usually a bank or online store, will tell you that there is a problem with your account. If links appear in this kind of e-mail message, never click on them regardless of how “believable” they seem or who the source is. If you have an account with the organization, it’s better to call your service representative and verify the authenticity of the e-mail. If it is legitimate, ask to complete the process by phone. This eliminates the need to send your sensitive data over unprotected networks.
OWASP foundation has treated this vulnerability with acute seriousness and ranked them as NO. 6 in their Top 10 list of 2013.
The Table below depicts the OWASP foundation’s view on ‘Sensitive Data Exposure’:
| Threat Agents | Attack Vectors | Security Weakness | Technical Impacts | Business Impacts | |
| Application Specific | Exploitability AVERAGE |
Prevalence WIDESPREAD |
Detectability AVERAGE |
Impact SEVERE |
Application / Business Specific |
| Consider who can gain access to your sensitive data and any backups of that data. This includes the data at rest, in transit, and even in your customers’ browsers. Include both external and internal threats. | Attackers typically don’t break crypto directly. They break something else, such as steal keys, do man-in-the-middle attacks, or steal clear text data off the server, while in transit, or from the user’s browser. | The most common flaw is simply not encrypting sensitive data. When crypto is employed, weak key generation and management, and weak algorithm usage are common, particularly weak password hashing techniques. Browser weaknesses are very common and easy to detect, but hard to exploit on a large scale. External attackers have difficulty detecting server-side flaws due to limited access and they are also usually hard to exploit. | Failure frequently compromises all data that should have been protected. Typically, this information includes sensitive data such as health records, credentials, personal data, credit cards, etc | Consider the business value of the lost data and impact on your reputation. What is your legal liability if this data is exposed? Also, consider the damage to your reputation. | |
Are You Vulnerable To ‘Sensitive Data Exposure’?
The first thing you have to determine is which data is sensitive enough to require extra protection. For example, passwords, credit card numbers, health records, and personal information should be protected. For all such data:
- Is any of this data stored in clear text long term, including backups of this data?
- Is any of this data transmitted in clear text, internally or externally? Internet traffic is especially dangerous.
- Are any old/weak cryptographic algorithms used?
- Are weak crypto keys generated, or is proper key management or rotation missing?
- Are any browser security directives or headers missing when sensitive data is provided by / sent to the browser?
How To Prevent ‘Sensitive Data Exposure’?
- Considering the threats you plan to protect this data from (e.g., insider attack, external user), make sure you encrypt all sensitive data at rest and in transit in a manner that defends against these threats.
- Don’t store sensitive data unnecessarily. Discard it as soon as possible. Data you don’t have can’t be stolen.
- Ensure strong standard algorithms and strong keys are used, and proper key management is in place.
- Ensure passwords are stored with an algorithm specifically designed for password protection,
- Disable autocomplete on forms collecting sensitive data and disable caching for pages that contain sensitive data.
- Consult Information Security Experts for detailed and thorough checks of all sensitive web applications.
- Consider investing in DLP solutions or for Web Applications a WAF with custom rules (mask credit card numbers, SIN numbers) with targeted policies to prevent sensitive data exposure to clients
Sources: OWASP, Wikipedia and Indusface Internal Analysis
Stay tuned for more relevant and interesting security articles. Follow Indusface on Facebook, Twitter, and LinkedIn.
