OWASP Top 10 2021: Vulnerabilities & Mitigation Guide
Read on to find out the OWASP Top 10 vulnerabilities 2021 explained in detail, along with ways to…
5 articles

Read on to find out the OWASP Top 10 vulnerabilities 2021 explained in detail, along with ways to…

A serialization attack exploits vulnerabilities in serialization processes to manipulate data or gain unauthorized access, posing significant security…
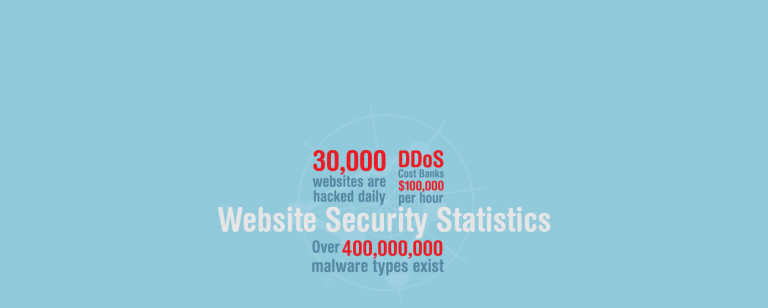
Did you know that 155 .GOV and .NIC domains were hacked last year? Learn about more of such…

Attackers may steal or modify such weakly protected data to conduct credit card fraud, identity theft, or other…

To prevent Broken Authentication vulnerability, use strong password policies, implement multi-factor authentication, and regularly monitor user activity.