“An internet connection is all the infrastructure that you need.”
A few years ago, outsourcing was largely limited to customer relationship management, human resource management, procurement solutions, and team collaboration. However, the increasing complexity of handling information security operations, especially web application security, has made businesses rethink what needs to be outsourced.
From a security perspective, it is critical to cover each layer of the Open Systems Interconnection model (OSI Model), which consists of physical, Data Link, Network, Transport, Session, Presentation, and Application layers.
Although ensuring security within layers from physical to the presentation is simpler for in-house teams, it’s not the same with Application aka Layer 7. This layer alone is a target of 75% of the hacking attempts all over the world and it takes distinct expertise, awareness, and understanding to prevent such attempts.
Business and government entities can always hire an in-house web application security and monitoring team, but it often comes down to the time and money spent on management and organization. Far more often, it even takes the focus away from key business activities, diluting what could have been achieved with that time and money otherwise.
This is exactly the kind of hiatus between requirement and fulfillment bridged by software as a service (SaaS). It allows organizations to unload their AppSec worries to niche players while still maintaining close control over what needs to be done.
While a lot of people have already accepted SaaS-based web application security as a necessary shift, others have apprehensions about costs and loss of control over security, most of which we will be talking about here.
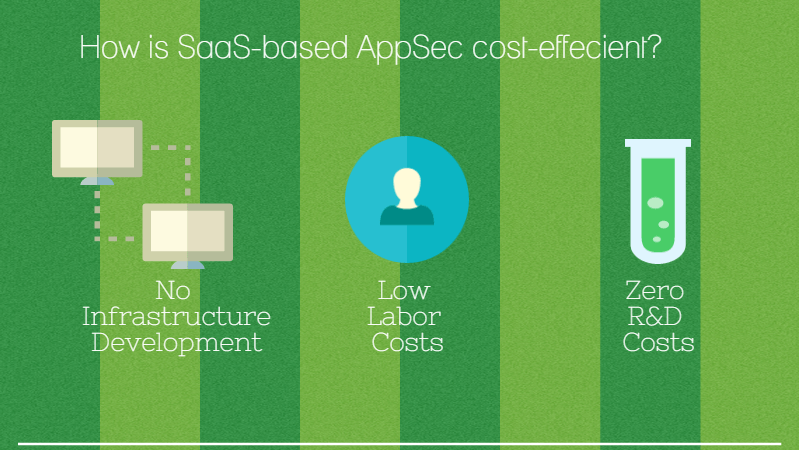
How is SaaS-based web application security cost-efficient?
A simpler and more prevalent answer would be the money you’d be saving by not using the hardware, software licenses, web application firewall installation, information, and technology labor, and security analysts along with people to monitor, manage, research, and provide internal downtime support.
However, this usually doesn’t provide a clear picture of what exactly businesses can save. That’s where a study conducted by Forrester Research provides valuable insights into the costs that a company will have to incur for initial configuration and then for years to come.
Surprisingly, they have estimated that cost, which includes labor costs for log management, labor costs for threat research and monitoring, infrastructure, and downtime response, comes to around $275,000 followed by a similar annual amount in a risk-adjusted model.
Now for any business, it is a huge added investment assigned to a single security vector. However, problems do not end with just the cost. Even after spending so much, you cannot be sure if the in-house AppSec standards are at par with the industry or if there is still a risk of a breach.
Additionally, the AppSec domain is extremely volatile. Zero-day threats, vulnerability vectors, and new security patches have to be followed diligently for keeping risks at bay.
This is exactly why SaaS-based web application security is getting immensely popular. Vendors offering such services have ready-to-deploy, cloud-based options that can be integrated with existing security architecture. This way, companies do not need to employ security personnel separately, manage training, and fund research & development consistently.
If you take Indusface’s suite of products here as an example, the total application security that detects, protects, and monitors consist of Web Application Scanner (WAS), and Web Application Firewall, backed with expert monitoring and tuning. The initial cost of such an option is zero followed by annual subscriptions. If you compare its annual subscription versus in-house annual web application security, the difference is astounding.
How do get over the apprehensions towards SaaS-based web application security?
Although the benefits of the software-as-a-service application security model are obvious, money is not always the topmost priority for most institutions including government entities. Their data is far more valuable and under no circumstances, they can afford to lose important details about website security and its vulnerabilities.
Additionally, the remote security vendor option also brings the fears of loss of control. In most cases these apprehensions are logical, that is why we bring you a guide that can help pick a better security partner.
Partner with expert monitored and managed web application security
Web application scanners and web application firewalls are the most important foundations of AppSec. However, these tools are not more than simple automated machines designed to follow rules, if not backed by experienced security professionals. They aid in proper rule modulation, alerting, and real-time response in case of critical situations. Organizations should ideally look to partner with app security vendors that offer continuous monitoring, custom rule policing, and ongoing management by experts.
Bid for control and usability
Application security functions are often futile if they are do not translate into clear benefits and control. It is important that you get important information on a neat platform about what’s happening, how many attacks were mitigated, and what rules are in effect. It helps you synchronize application security with overall security and make informed decisions. Look for web application security options that put you in control of app security with a neat dashboard control.
Ask for high uptime and fail-open
How good is a web application firewall or web application scanner if it’s down to maintenance half of the instances? Enterprise CIOs and CISOs have strong preferences for uptime percentages and there’s every reason that every business owner should ask for it. It ensures that you stay protected round the clock. High uptime backed with disaster recovery and fail-open models ensure business continuity even in extreme conditions.
Maintain accuracy
Did you know that false positive is one of the most frustrating issues with security products? It’s a false alarm that consumes both time and money looking for a problem that was never there. Due to the complexity of web application firewall rule modulation, it is the topmost concern today.
Look for zero false positives with your web application firewall to reduce log monitoring redundancy and to focus more on real incidences.
