What is a Slowloris DDoS Attack?
A Slowloris attack is a type of denial-of-service (DoS) attack that overwhelms a web server by keeping numerous connections open indefinitely.
In a Slowloris DoS attack, the attacker sends many HTTP requests to the target web server, but unlike a regular DDoS attack, the requests are sent slowly over a long period of time.
The attack sends incomplete HTTP requests to keep the connections open for as long as possible. The attacker then mimics this pattern by sending many incomplete requests to the server. By doing this, the attacker consumes the server’s memory and CPU as it tries to keep track of all the open connections. Eventually, the server becomes overwhelmed and can no longer respond to legitimate requests.
Examples of Slowloris Attacks
There have been several high-profile Slowloris attacks over the years. Here are a few examples:
- In 2009, Iran accused the US of launching Slowloris attacks against its government websites. The attack lasted for several weeks and caused significant disruption to the targeted sites.
- In 2011, the website of the CIA was reportedly targeted by a Slowloris attack by the hacker group LulzSec. The attack caused the website to be unavailable for several hours.
- In 2018, a Slowloris attack was launched against several banks in Russia, causing their websites to become inaccessible. The attack was reportedly carried out by a group of hackers known as MoneyTaker.
How is a Slowloris DDoS attack different when compared to a traditional application DDoS attack?
Slowloris DDoS attacks are different from traditional DDoS attacks in a couple of ways.
First, in a traditional application DDoS attack, the attacker floods the target with a huge number of requests, typically from botnets. These requests can be legitimate or malicious and are designed to overwhelm the target’s resources, such as memory or CPU.
In contrast, in a Slowloris attack, the attacker sends a relatively small number of requests but does so slowly and incrementally. These requests consume the target’s resources over a longer period of time. The requests are typically incomplete, with the attacker deliberately keeping the connection open by sending partial requests or delaying sending the next request.
Finally, traditional application DDoS attacks are often detected and mitigated by WAFs or intrusion prevention systems, while Slowloris attacks can be more difficult to detect and block. The attack traffic may not appear malicious, and the server may appear functioning normally, even when overloaded with open connections.
Slowloris Attack Vs. UDP Flood Vs. SYN Flood Vs. Ping of Death
| Types of Attacks | Method | Objective | Layer of Operation | Targets | Stealth and Detection |
| Slowloris Attack | Keeps numerous connections open to a web server with incomplete HTTP requests, gradually consuming server resources. | Overwhelm the server’s resources, leading to a denial of service for legitimate users. | Application layer (Layer 7) of the OSI model. | Primarily effective against web servers. | More stealthy and harder to detect due to mimicking legitimate user behavior. |
| UDP Flood | Floods the target server with a high volume of UDP packets, targeting specific ports or services vulnerable to such attacks. | Overwhelm network resources, causing the server to become unresponsive to legitimate traffic. | Transport layer (Layer 4) of the OSI model. | Can target a wide range of services and protocols relying on UDP. | More straightforward and easily recognizable due to the volume of traffic generated. |
| SYN Flood | Floods the target server with a large number of TCP connection requests but doesn’t complete the connection handshake. | Fill the server’s connection queue with half-open connections, preventing it from accepting legitimate connections. | Transport layer (Layer 4) of the OSI model. | Any service or protocol relying on TCP, such as web servers. | Intense and rapid, aiming to quickly overwhelm the server’s capacity to handle new connections. |
| Ping of Death | Sends oversized or malformed ICMP packets to the target system, exploiting vulnerabilities in network protocol handling. | Crash or destabilize the target system by causing it to process malformed or oversized packets. | Network layer (Layer 3) of the OSI model. | Any system vulnerable to ICMP packet vulnerabilities. | Relatively rare in modern systems due to improvements in network protocol implementations. |
Why Are Slowloris DDoS Attacks Dangerous?
Slowloris DDoS attacks are dangerous because they can be carried out with relatively few resources and can effectively take down even large and robust web servers.
Slowloris attacks are called “slow” because they don’t rely on sending a high traffic volume like other DDoS attacks but rather on keeping a low-level stream of connections open for as long as possible.
As logs cannot be written until a request is completed, Slowloris can immobilize a server and go undetected for a long time. This happens without raising a red flag for anyone who actively monitors logs for any changes.
Because Slowloris attacks only require a small amount of bandwidth and can be carried out by a single machine, they are often difficult to detect and defend against.
Overall, Slowloris DDoS attacks are dangerous because they can be highly effective at taking down web servers, are difficult to detect and defend against, and can be launched with minimal resources.
Check out the best practices for preventing DDoS attacks here.
How Does a Slowloris Attack Work?
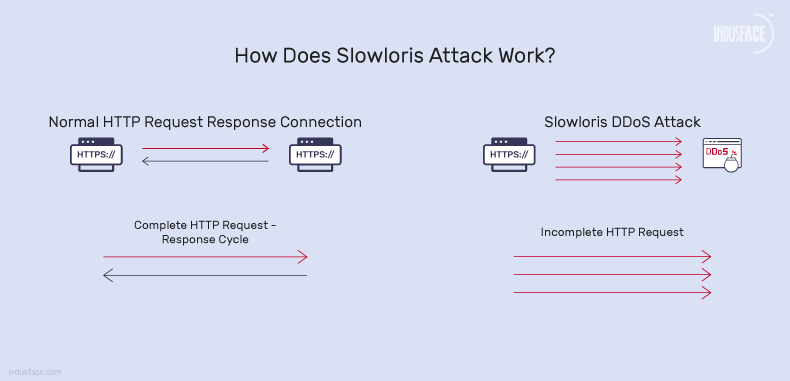
Here is a step-by-step process of how a Slowloris attack is carried out
- Connection Initiation: The attacker initiates connections to the target web server, just like a legitimate user would.
- Incomplete Requests: Instead of completing the HTTP requests quickly, the attacker sends partial HTTP requests to the server.
- Header Injection: Periodically, the attacker sends additional HTTP headers to the server, but doesn’t complete the requests by sending the necessary data.
- Persistent Connections: The attacker keeps these connections open by occasionally sending additional header lines, ensuring that the connections remain active.
- Resource Exhaustion: As the server is programmed to wait for the completion of these requests, each open connection consumes server resources such as sockets, memory, and processing power.
- Server Overload: With a large number of connections kept open simultaneously, the server’s resources become exhausted, and it’s unable to handle legitimate requests from other users.
- Denial of Service: Eventually, the server becomes overwhelmed and can no longer respond to legitimate user requests, effectively denying service to legitimate users.
- Persistence: Slowloris can maintain this attack for an extended period, as long as the attacker keeps sending periodic header updates to keep the connections alive.
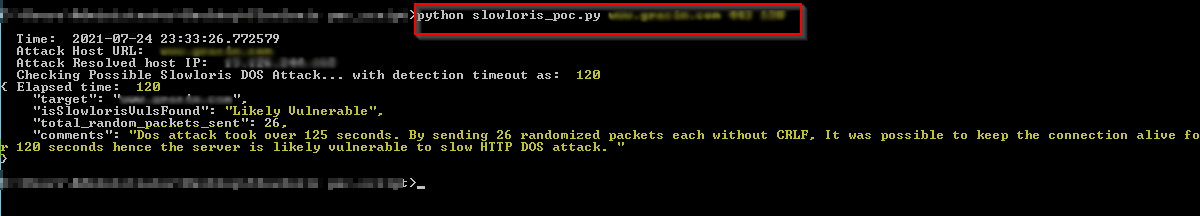
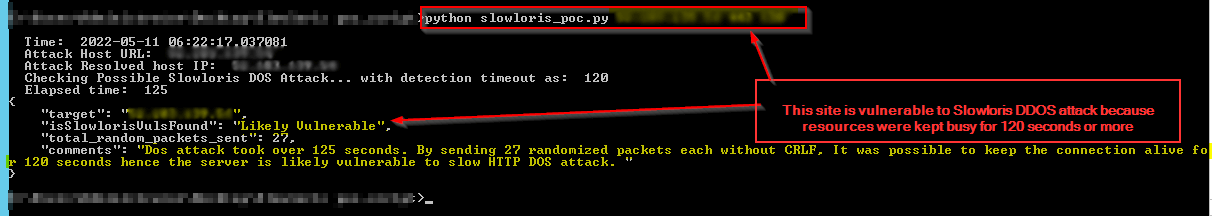
Here is an example of Slowloris attack:
Overall, the Slowloris DDoS attack exploits a vulnerability in how web servers handle connections, using a slow but persistent stream of partial requests to tie up server resources and make the server unavailable to legitimate users.
What are the Signs of Slowloris Attack?
In a Slowloris DDoS attack, the signs may not be immediately obvious since it’s designed to exploit vulnerabilities in how web servers handle connections rather than flooding the network with traffic. Here are some detailed signs to look out for:
Slow Website Response Times: Users may experience unusually slow loading times when accessing the website. This is because the attack aims to exhaust the available connections on the web server, leading to delays in processing legitimate requests.
Increased Server Resource Usage: As the attack progresses, you might notice a spike in server resource usage, particularly in terms of CPU and memory usage. This is because the web server is struggling to manage the large number of open connections initiated by the attacker.
Numerous Incomplete Connections: In the server logs, you may observe numerous incomplete connections from various IP addresses. These connections are part of the Slowloris attack, with the attacker deliberately opening multiple connections but not completing the HTTP request, tying up server resources.
Inability to Access the Website: In severe cases, the website may become completely inaccessible to legitimate users. This happens when the web server’s resources are fully consumed by the Slowloris attack, resulting in a denial of service for genuine visitors.
Unusual Network Traffic Patterns: Analyzing network traffic patterns may reveal an abnormal increase in the number of simultaneous connections from different IP addresses, especially if these connections are not completing typical HTTP requests.
Check out our blog for common DDoS symptoms here.
How to Detect a Slowloris DDoS Attack?
Here are effective ways to detect the DDoS attacks:
Monitoring Server Logs: Regularly review server logs for unusual patterns, such as an abnormal number of open connections from a single IP address or repeated connections without completing requests.
Network Traffic Analysis: Utilize network traffic analysis tools to monitor incoming and outgoing traffic patterns. Look for anomalies such as a high volume of partial HTTP requests or connections from the same source.
Connection Tracking: Keep track of open connections and their duration. Identify connections that remain open for an extended period without completing requests.
How to Mitigate a Slowloris DDoS Attack?
Here are six ways to mitigate a Slowloris DDoS attack:
1. Use a Reverse Proxy
A reverse proxy would act as a buffer between the server and clients, protecting the server from Slowloris attacks. The reverse proxy should ideally monitor incoming requests and drop connections that show signs of a Slowloris attack.
2. Limit # Connections Per IP
Limiting the number of connections that can be made from a single IP address would prevent the Slowloris attack. You could easily do this with a cloud WAF like AppTrana or a load balancer.
3. Reduce the Maximum Request Duration
Limiting the time a connection can be kept open would reduce the impact of a Slowloris attack. You could easily do this with a cloud WAF like AppTrana, a load balancer, or setting a timeout.
4. Implement Rate Limiting
By monitoring the number of connections and requests made to the server and limiting them to a reasonable threshold, the impact of a Slowloris attack can be mitigated. This can be achieved using software or hardware solutions, such as load balancers, firewalls, or intrusion prevention systems.
5. Keep Software and Systems Up-to-date
Keeping web server software and operating systems up to date can help prevent known vulnerabilities that Slowloris attacks can exploit. Leverage a DAST scanner like Indusface WAS to find all open vulnerabilities categorized by OWASP Top 10 and SANS 25.
6. Use a DDoS Mitigation Service
Specialized DDoS mitigation services can protect against Slowloris and other DDoS attacks. The AppTrana cloud WAF comes with bundled managed services to help you with custom rate limiting, traffic filtering, and traffic diversion to protect servers and networks from DDoS attacks.
Discover how AppTrana’s custom-built rules successfully thwarted a low and slow DDoS attack in our case study, here.
How does AppTrana Protect Against Slowloris Attacks?
AppTrana offers the industry’s only unmetered anti-DDoS solution backed by AI-based behavioural models that detect anomalies on site traffic. The cloud WAF also bundles managed services wherein cutting-edge technology is combined with the power of human expertise and intelligence of certified security professionals.
It is a comprehensive security solution that is custom-built with surgical accuracy based on the needs and risk profile of the business. AppTrana’s security services include infrastructure-level protection against volumetric Layer 3 and 4 attacks and always-on, instant protection against Layer 7 attacks by botnets and attacks like Slowloris on the application layer.
AppTrana monitors websites and web applications 24×7 to detect anomalous activities. The security experts continuously update the rules in real-time based on alerts to mitigate DDoS attacks and ensure web application/ website available at all times.
Stay tuned for more relevant and interesting security articles. Follow Indusface on Facebook, Twitter, and LinkedIn.