Today, more than 300, 000 websites are attacked daily and more than half of the attackers look for illicit financial gains. Quite clearly, Banking, Financial Services, and Insurance (collectively known as the BFSI) become obvious targets for exploitations around the world. Although we have already talked about the risks involved with online payment security in one of the previous blog posts, an increase in Layer 7 attacks through the last year has made our researchers look into the common application security challenges and future of the BFSI sector. So, how to secure a website?
Secure Banking Website Challenges
a) Regulatory Compliance
When it comes to dealing with card payments, every website in every sector is governed by a strict standard comprising of laws and regulations known as the Payment Card Industry Data Security Standard. It is the most trusted information security standard across the world and requires annual validation evaluated on the security structure of the website across different layers.
Similarly, the Reserve Bank of India is also closely involved in information security, electronic banking, technology risk management, and cyber frauds. In fact, RBI guidelines emphasize the importance of risk assessment and audits. Their application control and security outlook further clarify how apps should be designed, developed, audited, and monitored. IRDA and SEBI have similar strong concerns on how they would like to see the Insurance and Broking websites handling security too.
Now, along with maintaining a high level of user experience and offering a wide array of services, BFSI domain organizations find it difficult to mandate a compliance structure and adhere to these guidelines with frequent changes.
b) Security Prioritization
The domain of online business, including the BFSI sector, is flooded with competition, which often leads to frequent application changes for better services, scalability, and conversions. And to be honest, security isn’t exactly on the top of the minds of management and developers of these websites. They are rather keen to offer more creative application options that meet business activity requirements better.
Additionally, developers are also under pressure to meet regular application project deadlines rather than concentrating on how to secure a website and understanding application vulnerabilities beyond compliance. Under such circumstances, app security lags behind increasing the chance of exploitation and manipulating within the code framework.
c) Security Staff Management
Hiring, managing, and retaining cybersecurity people, especially application security personnel, are not even remotely easy tasks. They require a different mindset, allocation of resources, and several other efforts that might prove to be a distraction in regular business activities.
It is also inappropriate to handover the entire website security portfolio to third-party service providers.
Who is to make sure that they will not misemploy the provided information? Who is to blame if all of a sudden their security mechanisms go down?
d) User Experience Optimization
Imagine a payment platform that doesn’t ask for a card or CVV number every time someone makes a transaction. It stores data and even online transaction passwords, making the process 10 times faster. Users will definitely love it, but it will also be a security nightmare. That how security and UX can be inversely proportional. Although in real-life scenarios contrast is not that high, application coders do have to balance the act.
Where management and conversion experts push applications towards simplicity and ease of use, coders struggle with maintaining the highest levels of security protocols with the user experience and conversion changes. Having said that, conversions and simplicity aren’t evil, it’s just a matter of having a technology that can back it up with smart user behavior baseline policies.
e) Low App Security Budgets
Chief Information Security Officers (CISOs) in the BFSI domain have limited resources to work with. They have to utilize the allocated budget to secure multiple layers in the Open Systems Interconnection model and often it’s not enough to test application vulnerabilities and to develop patches for them. In fact, according to a study from the Ponemon Institute, only 18% security budget is allocated to app sec while Gartner says that 75% of the attacks happen at the application layer.
Given that Layer 7 is vulnerable to code injection, session hijacking, authentication cracking, and other OWASP attacks, there is little that security professionals can do about it with low budgets. Over time, this domain has repetitively called for options that can highlight and shield vulnerabilities in real-time before CISO can approve a budget for the applicable patch.
BFSI Future
Banking, Financial Services, and Insurance, as an industry, has huge potential for growth in the coming years. In a way, if you look at it, people are only going to transact online if they think that their identity and money are safe through the banking and financial institution channels. Therefore, it is more of a responsibility to ensure security when future applications are set to become even more complex and attacked more often in state-funded cyber warfare.
- BFSI will be the prime target for financial gains.
- The web application will get more complex with frequent updates.
- Public sector institutions will be attacked by state-funded cyber black ops.
We believe that in the coming years, there will be a much greater need for security solutions that can patch security loopholes while providing a higher level of control and scalability.
Indusface Stance
As the trusted application security partner for 9 out of the top 10 banks in India along with several other big names in the BFSI sector, we have tested some 10,000 odd applications and have performed over 2.9 million application vulnerability scans. During this time, we have realized that the most important element for financial institutions is to have a complete security package on the table rather than the option of sourcing fragments from multiple vendors.
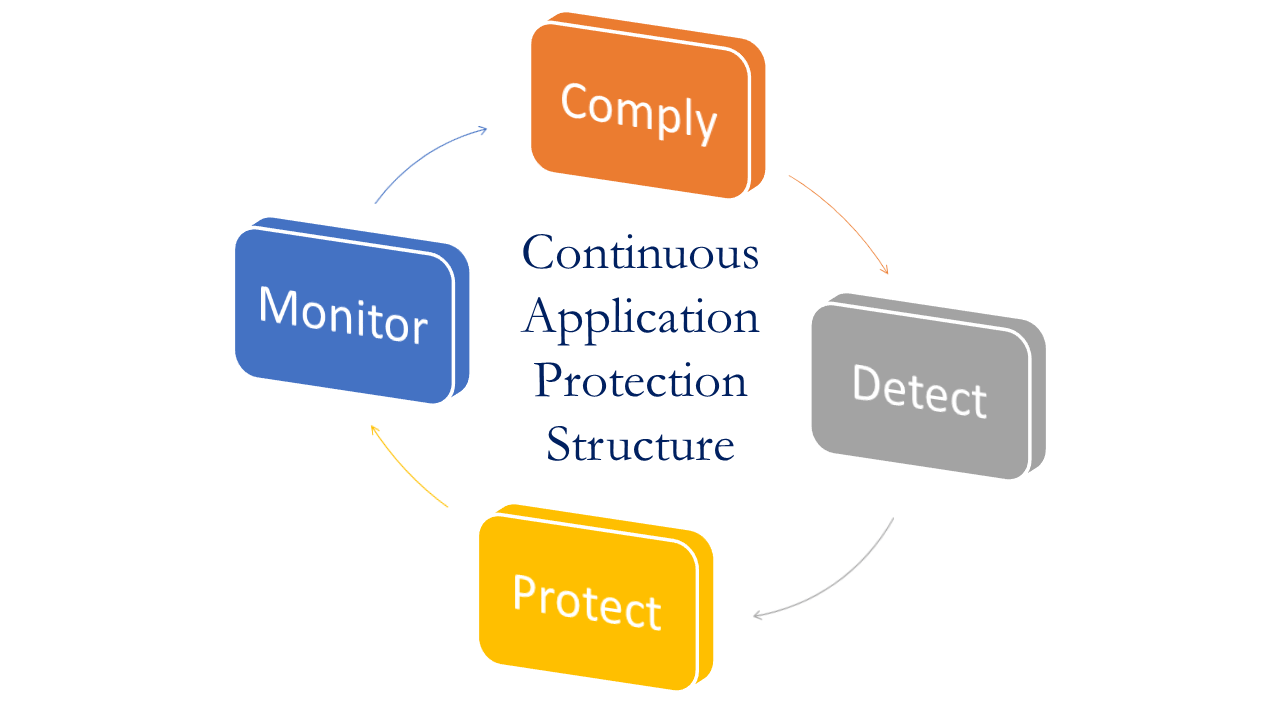
That’s where our philosophy to detect, protect, and monitor allows organizations to deploy testing, mitigating, and controlling options conveniently. This way, companies do not have to train and manage dedicated application security staff and still maintain extremely high uptime rates at the pay-as-you-go model.
Furthermore, the Indusface Vulnerability Scanning, malware monitoring, mobile application security, web application firewall, and source code review backed by Service Level Agreement.
We take pride in helping organizations meet stringent regulatory compliance guidelines, seamlessly prioritize security, and cut application security costs with a one-of-a-kind SECaaS model.
Stay tuned for more relevant and interesting security articles. Follow Indusface on Facebook, Twitter, and LinkedIn.
