My DDoS Story
If you are acquainted with the popular OWASP Series (Part 1, 2, 3, and 4), you probably also have heard of Frank and the strange security issues he was faced after the recent website and mobile app launch.
Finally, when everything was looking right at the Fishery of Randomland, they landed up in one of the biggest troubles so far.
‘There is so much traffic on our website, people love our fish,’ a happy marketing manager at the Fishery of Randomland shouted that day.
Their website was getting 7 times the traffic they usually get in a month, all of it in a few hours.
Day 1: Realization
Business as usual around Christmas time. Some fish sold, some delivery troubles, and loads of phone calls to find out more about the big sale day they were having in 2016. Frank, the owner at the Fishery of Randomland, received what sounded like an over-excited call from his team.
They were elated about the fact that people were filling shopping carts with all kinds of fish on the website. Their overall traffic was exponential.
‘Wow, who’s buying? How many sales did we make,” Frank asked the real question.
The phone line went silent for a brief moment before it was reluctantly answered with a confused tone ‘No sales yet sir’.
Frank rushed to the department looking for some traffic data. Interestingly, no sales were actually made while the application developers failed to answer why so many carts were still loaded with orders without any sign of payment.
They dug deeper to realize that actually none of the traffic was actually coming from Randomland. Cities far away like Devil and Darkland were all over the website. Places where Fishery of Randomland did not even sell.
In a while, customer service phones started ringing relentlessly. Worried actual customers from Randomland wanted to fish for the Christmas celebration. They couldn’t get to the website. It was down and out.
Frank and others at his office could understand something was wrong but they didn’t know what it was until an email notification popped.

The website going down right at Christmas time, was there nothing they could have done differently? Frank knew that it was not just a matter of 200,000 or keeping customers waiting for an entire day. There were 50 more fish sellers waiting to take their businesses. Customers would move on, and many of them will never come back slashing customer lifetime values in half or low. What if it happens again? Will he keep paying hundreds of thousands to these kinds of attackers? Frank had a lot to think about that day.
Day 2: Reaction
No matter what they did, there was no relief. Sometime around three in the morning, when everyone was gone realizing that they cannot do anything about it, Frank thought of something. His entire life was about getting things on his terms. Why should the incident be any different? That’s the moment when he realized that no one else could decide when he can run his business.
‘Need some help Ralph,’ Frank called his trusted security advisor once again. He realized that this should have been done earlier. After all, Ralph usually has the answers.
‘Looks like an application DDoS attack,’ Ralph drove quickly to their offices.
‘An application what?’ Although Frank had heard of DDoS, he wasn’t sure if it happens on applications too.
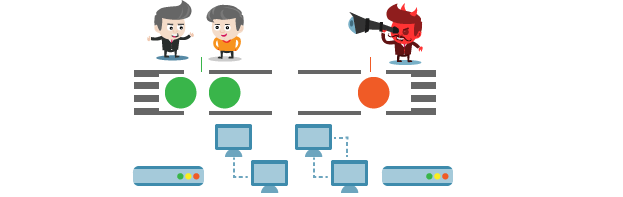
‘Imagine a shop suddenly filled by 45,000 robots at once. This way you’re actually customers who cannot enter the shop. It’s Distributed Denial of Service (DDoS),’ Ralph drew it all on paper to make things simpler.
‘I know what it is, but why is it happening on our shopping applications,’ puzzled Frank asked.
‘Think for yourself. It’s efficient. Your entire business runs on applications, it’s obvious to attack those,”
‘But why?”
‘This time it’s money in return. Other times, it can be your competition or maybe an employee who isn’t happy. Why not when enormous bot traffic is available for just $5 for an hour,’ said Ralph.
‘I’m assuming that you have a solution to this problem, a problem that I feel will keep coming back,’ Frank was slightly relieved now.
‘One, someone needs to study your traffic sources in terms of geographical locations, machine IDs, IPs and henceforth. This is just a start, once the red flags are raised, the security team should be able to stop spam/bot traffic to applications efficiently. It has to happen ceaselessly day and night if you don’t want the server to crash and website to go down. And amongst all this, you have to make sure that this arrangement is not blocking real customers from Randomland or those traveling to Darkland but mean to purchase,’ Ralph sounded like he had dealt with some of these.
‘Sounds like a lot of work,’
Of course neither Frank nor his developers had the time for nitpicking. They had a business to run, and with New Year’s Eve coming, things had to get busy. But Frank his trusted security advisor configure the web application firewall so that both Frank’s team and Ralph had access to traffic analytics. If WAF showed alerts, Frank’s team could block traffic temporarily from suggested machines. And Ralph was always a call away to look at it and make things right. And yeah, Fishery of Randomland didn’t pay 200,000 that day, or any other day.
Simple Application DDoS Blocking
Frank is definitely not the only one with distributed denial-of-service attacks on applications. Figures show that it has grown drastically over the last couple of years. Banks, retailers, and digital businesses are most vulnerable to it, given the value of being ‘always there for the customers, or else it doesn’t take much time for them to move on.
Indusface introduces the Total Application Security (TAS) that in addition to finding issues and blocking hacking attempts, is also equipped to handle basic and advanced DDoS attempts on applications. Backed by a dedicated security team for every website, it allows you to take security control. Experts can provide you actionable data, insights, and suggestions, which you can use to block DDoS attacks yourself through the dashboard or ask them to do it for you.
Find out how to get DDoS protection that is always there for you.


 May 17, 2016
May 17, 2016




