31 Google URLs Vulnerable to Open Redirect
Do you remember the last time we discussed OWASP A10- Invalidated Redirects and Forwards? It was our OWASP…
161 articles
Do you remember the last time we discussed OWASP A10- Invalidated Redirects and Forwards? It was our OWASP…

cybersecurity questions to few of our readers and cybersecurity experts. Here are a few of them. Question 1…

Banking, ecommerce, and a number of other websites increasingly offer spreadsheet export functionality within their applications to help…

How do you secure website from hackers? Look at some of the expert tips and ensure that hackers…

The current ‘automating everything’ approach for application security shouldn’t be just replaced. It should be buried down under…
With rising number of security lapses, the question is inevitable. While many companies understand the importance and need…

Badlock is referenced for Microsoft Windows by CVE-2016-0128 / MS16-047 (Windows SAM and LSAD Downgrade Vulnerability) and for…
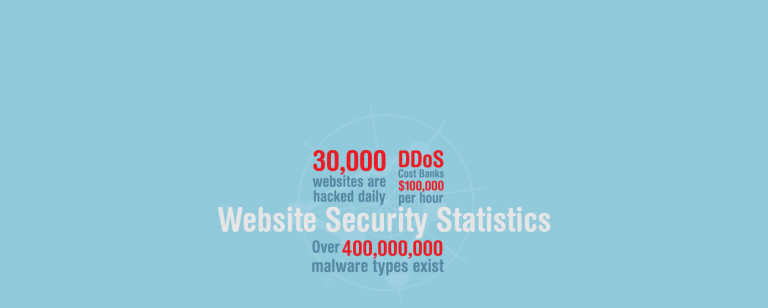
In 1996, nine years after the launch of the World Wide Web Project, number of websites had grown…

Do you know about the recent bank cyber heist attempt in Bangladesh? Apparently, hackers tried to steal $951…

DROWN allows hackers to decrypt browser-server communication in hours to attack servers or/and users. Shockingly, this newly found…
Did you know that 155 .GOV and .NIC domains were hacked last year? Learn about more of such…
Somewhere in October, NASSCOM-DSCI closed nominations for the Excellence Award. From there, read Indusface’s journey to Emerging IS…