Understanding Serialization Attacks: Risks, Examples, and Prevention
A serialization attack exploits vulnerabilities in serialization processes to manipulate data or gain unauthorized access, posing significant security…
8 articles

A serialization attack exploits vulnerabilities in serialization processes to manipulate data or gain unauthorized access, posing significant security…

Flagstar Bank, recently confirmed a data breach that exposed the sensitive details of 1.5 million customers. Read more.

There are several things you can do to protect your business from data breaches. Here are the 3…

“Application breaches every other day” has been the unfortunate reality of 2019. As the year draws to a…
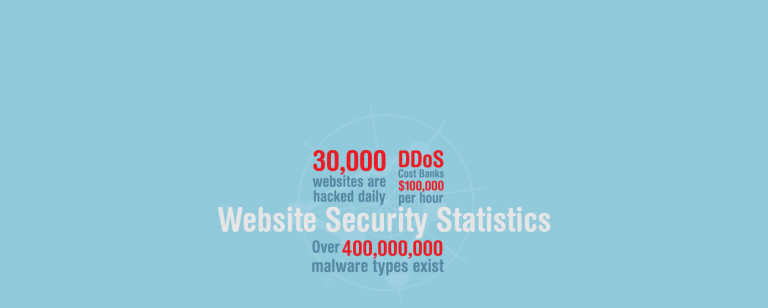
Did you know that 155 .GOV and .NIC domains were hacked last year? Learn about more of such…
Data breach affects more than just data. The consequential damages will hit you for the years to come…

Data breaches result in loss of customer trust and heavy financial damage, but for startups it’s about survival.…

Hackers around the world are making big money by just selling stolen data. Find out how these data…