Keeping your startup safe from hackers, data loss and breaches takes more than just a firewall and antivirus software. Hacking has become a serious – and expensive – global problem that has destroyed the reputations and finances of small businesses and corporations alike.
Cyberattacks against small and medium businesses account for 50%. And the cybercrimes weren’t just hackers using sophisticated tools to break into company’s cybersecurity, data files and servers. Negligent employees, contractors, and third parties actually caused most of the data breaches.
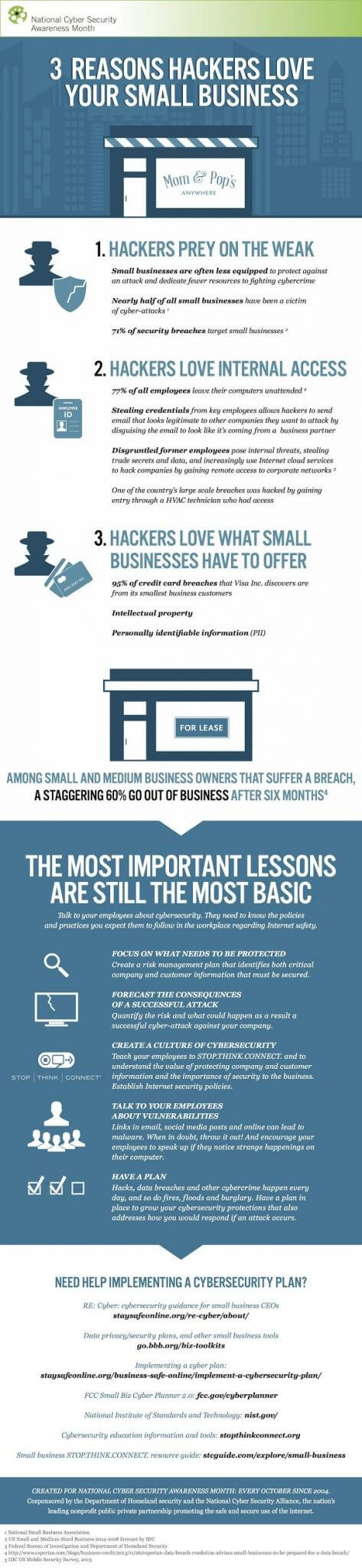
Although big corporations are frequently hit by hackers, small businesses are especially at risk. Have you ever wondered why hackers love small businesses so much?
Small Business are a Target of Cybercrime
Unfortunately, smaller companies are easier to hack because they have little experience with the kind of cybersecurity required to combat the ever-growing legion of sophisticated hackers.
According to the Ponemon Institute, cyberattacks directed at SMBs are rising globally, nearly 45% of small and medium-sized businesses surveyed reported their security posture as ineffective, and 39% said they have no incident response plan.
Startups are also usually allocating any available cash toward growing their businesses instead of protecting them. But waiting until something happens can cost companies their livelihoods. According to reporting by the New York Times, the effects of ransomware on small businesses can cause catastrophic loss and often force them to close their doors.
First impressions in the online world are absolutely everything and can make or break a company. In a world where missteps and bad customer service experiences go viral, companies can’t afford to wait until getting hacked to do something about their cybersecurity. A major corporation with a longstanding good reputation in their industry and loyal customers may be able to restore consumer confidence after a data breach, but startups rarely have that same type of consumer currency in place.
Sixty percent of small companies that were hacked were out of business within just six months. But even huge corporations that have been hacked and manage to recover their reputations and sales pay a price. Target’s massive data breach exposing consumer credit card information resulted in over 140 related lawsuits and the resignation of its CEO.
Consequences of Cyberattack
The consequences of a hack are complicated, time-consuming, and costly, and can ultimately close businesses. Rokenbok, a startup using blocks and robotics to teach children to think like engineers, lost thousands in sales when its data was held for ransom by hackers. Rokenbok database files were infected with malware – and it wasn’t the company’s first experience with the hacking that ultimately shut down its website.
Yahoo drew intense criticism when it was discovered that the company waited years to admit to a massive hack. In an interview with CNBC, Experian vice president of Fraud & Identity product strategy Matt Ehrlich said, “Every day [a breach] goes undetected, unchecked, that’s going to escalate damage.”
Instant messaging and collaboration system Slack suffered a database breach that exposed customer user names, email addresses, phone numbers, and Skype IDs. Slack’s reputation took a public nosedive. Little wonder, since Slack’s entire sales pitch is based on the idea that businesses using Slack can eliminate email and trust the platform with all their sensitive and highly-confidential conversations instead.
There are also investment implications to consider when it comes to hacking. Your startup can’t survive looking for funding if investors see it as an insecure entity. And if you’re an existing company, your stock could wind up in freefall. Twitter’s stock price plunged by 4% after hacking incident.
Here are some insights from HIPAA Secure Now
The Threats

Companies that think they’re ready for a hack need to rethink their strategy. Savvy startups may assume they already know the pervasiveness of malware and how to protect themselves; they may think phishing scams over email are easy enough to spot, and simply avoid any links from unknown senders.
In reality, there are much bigger threats waiting on the cybersecurity horizon. For starters, the security of the IoT is predicted to become a life-threatening issue. Device security for the IoT, especially in the medical and healthcare fields, is mostly an afterthought. But the implications of what could actually happen are shocking. Consider how IoT devices handle sensitive information and tasks like releasing life-saving medicine via an insulin pump. There could also be issues with entire power grids or transportation systems being hacked and taken down after a device connected to the IoT is hacked and compromised.
Your startup may not need to worry about that just yet, but the reliance on mobile devices and applications leaves all businesses vulnerable. Mobile points of entry are unsurprisingly common for cyber attacks. These malicious attacks could ultimately impact mobile payments. But it’s not the hackers who will have to pay the price. Data loss and financial damage from hackers ultimately means businesses are held accountable to their customers.
How to Respond if you’ve been Hacked?

Hackers are ingenious at finding ways into data files and devices, and chances are incredibly high that you may still have to deal with a cyber-attack at your business. We’ve witnessed a lot of right and wrong ways to respond to hacking, and how to react when public pressure is on. So how should your company respond?
- React quickly and inform those affected, from employees to customers. In other words, don’t pull a Yahoo and wait years to let your customers know their accounts were compromised.
- File a notice of the breach if required, and comply with industry regulatory agencies if necessary.
- Thoroughly examine the hack in minute detail, and bring in cybersecurity experts or have your in-house IT team implement your response plan.
- Launch a response plan as quickly as possible – and if you don’t have one already, create one now. Whatever you do, don’t wait for a hack to put one together.
- Plug the leak. Revoke devices until you can figure out how to protect them – especially if you discover the hack came from the unprotected device of an employee who is prone to using public WiFi and downloading third-party apps.
- Consider hiring a cybersecurity expert to perform penetration testing to see where your company’s systems are the most vulnerable.
11 Cybersecurity Best Practices
1. Be Proactive

The best way to survive a hack is to stop hackers in their tracks. Stay proactive and prevent damage before issues with malware and ransomware spiral out of control. Be diligent about your company’s security, and get your entire team involved in the process. Here are some best practices to implement to keep your business secure:
2. Monitor your Social Media Accounts
It’s all too easy to get caught up in social media and fill out public-facing Facebook profiles with the names of your kids, pets, and other personal indicators. Keep any personal information that could help hackers crack passcodes off of social media altogether.
Next, monitor your social media accounts and watch for suspicious behavior and posts. Don’t assume that you must have accidentally reposted a commercial message about a product. Immediately delete the post and change your password just in case. It’s also crucial to your company’s security never to use duplicate passwords across multiple social media accounts. Each one should be unique and complicated.
3. Get the Right Tools
Startups using multiple apps, cloud-based tools, and mobile devices need a comprehensive one-stop shop to deal with their security issues and protect them from a hack. Remember that the best offense is a good defense and requires the right tools. For example, Indusface offers web application scanning, web application firewalls, mobile penetration testing, and SSL certificates to manage a startup’s security service needs.
4. Have a Written Security Policy
It’s not enough to simply know how your startup will react during a security breach or hacking episode. This isn’t information to keep in your head or talk about in passing at a company meeting.
Your startup needs a written security policy covering all the possible scenarios of a hack – and how to respond – that’s readily available to all employees. Go over the material periodically and brush up on security procedures. In the event of a hack, use the security policy as a checklist to ensure standards are being met.
5. Create a Culture of Cybersecurity
In theory, employees understand that passwords should be kept secure and updated on an ongoing basis. They may also say they only download apps from trusted providers and app creators. In reality, most people are negligent and complacent with their password maintenance, aren’t diligent about researching their apps, and don’t stay on top of the latest trends in hacking. Hold monthly or quarterly meetings to familiarize employees with cybersecurity best practices, latest threats, and using 2FA to protect passwords. After each session, sharing a complete Zoom meeting summary can help employees quickly revisit key points and stay on top of important guidelines.
Encourage employees to take extreme caution with their devices, especially those that mix their personal and work lives (or devices). Super-hacker-turned-ethical-hacker Kevin Mitnick works with Fortune 500 companies and governments to hack into their systems and report on their vulnerabilities. He advises using longer passwords than the standard four-character codes to unlock smartphones. He also warns that public WiFi in cafes and airports can be easily cracked by hackers. One often overlooked vulnerability is fragmented communication channels. When teams default to personal WhatsApp groups, unofficial Slack channels, or texting clients directly, sensitive business data scatters across unmonitored platforms. A dedicated business phone centralizes communications under IT oversight – so client conversations, access codes, and sensitive discussions stay within systems you can audit, encrypt, and revoke access to if needed.
6. Stay on Top of Hacking Trends
Today’s most popular ransomware and malware attacks may be gone tomorrow and replaced by something even more malicious and destructive. Don’t wait for a hack to happen to your startup before you learn about new and emerging risks.
Keep an eye on cybersecurity blogs and stay on top of all emerging and existing threats. This is important even if you think an issue like IoT hacking won’t impact your company. In reality, hacking sends ripples around the world and can be mimicked and developed to spread to new industries.
7. Update your Systems
Startups using outdated systems and technology are highly susceptible to hacking. Outdated technology and POS systems were the culprits in Wendy’s infamous hack, ripping through 1,000 franchises and compromising thousands of customers’ credit card data. Your customers are relying on you to keep their data and financials safe, and that’s impossible to do without updated systems and software. Mark a day on the calendar to regularly check that all employees have updated their own systems and software to further a culture of security in your startup.
8. Restrict Data Access
Startups without experience in cybersecurity, and that are working on lean principles and skeleton crews, are susceptible to disorganized data. Take a look at who is accessing data and why, and restrict all employee and third-party access to sensitive data unless absolutely necessary. There is really no reason to allow data access to everyone on your team unless it’s absolutely crucial to their role.
9. Backup and Encrypt your Data
Always back up and encrypt all of your data and store it in a safe location. These techniques can help cut ransomware off before it causes too much damage. If a hacker holds your data for ransom, you have the option to wipe your devices and start over with new ones. From there, you can restore your data.
Encrypting your data also helps keep hackers from being able to crack open any stolen data. It may be your customers’ and employees’ only shot at staying safe in the event of a hack.
10. Prepare for Failure
Nothing is foolproof when it comes to cybercrimes and malware. Even the most secure businesses are sometimes hacked, and those that come out of a hack with their reputations and customers intact have a plan of action. Preparing for failure just means your startup is staying ever-diligent about its security, staying on top of hacking trends, and constantly testing and examining security policies and best practices to stay as safe as possible.
11. Engage with Cybersecurity Experts
The success of startups relies on speed and agility, and spending time and resources on security can get in the way of this speed. Instead of trying to build all the skillsets in-house to manage security, outsource to others for their app cybersecurity expertise like Indusface, to help you identify risks and protect you from those risks.
Conclusion
There is a silver lining when it comes to hackers. The constant threat of being hacked can keep your startup from getting too complacent about cybersecurity. Because when it comes to hacking, it’s wise to hope for the best but prepare for the worst. You still need to grow and run your company without the looming threat of hacking hanging over your head. Remember: hackers never discriminate, but if they did, they would actually prefer SMBs.
Need help protecting your startup? Get started today with a free trial with AppTrana.
