A critical vulnerability has been discovered in Angular Server-Side Rendering (SSR) that could allow attackers to manipulate request handling and trigger unauthorized server-side requests.
Tracked as CVE-2026-27739, the vulnerability arises from how Angular SSR reconstructs request origins using HTTP headers such as Host and X-Forwarded-*. In affected versions, these headers were not strictly validated before being used to build request URLs.
By supplying crafted header values, attackers may cause the application server to send requests to unintended destinations, including internal services or attacker-controlled endpoints. This behavior enables Server-Side Request Forgery (SSRF), potentially exposing internal resources accessible from the server environment.
What Is CVE-2026-27739?
Risk Analysis
Severity: CRITICAL
CVSS v4.x Base Score: 9.2
Vector: CVSS:4.0/AV:N/AC:L/AT:N/PR:N/UI:N/VC:H/VI:L/VA:N/SC:H/SI:L/SA:N
Exploit available in public: No
Exploit complexity: Low
Affected Product: Angular Server-Side Rendering (SSR)
Affected Packages:
- @angular/ssr
- @nguniversal/common
- @nguniversal/express-engine
Affected Versions: Angular versions prior to 21.2.0-rc.1, 21.1.5, 20.3.17, and 19.2.21
CVE-2026-27739 is a Server-Side Request Forgery (SSRF) vulnerability caused by improper validation of HTTP headers used during Angular’s SSR request handling process.
Angular SSR reconstructs the base URL of incoming requests using headers such as Host, X-Forwarded-Host, X-Forwarded-Proto, and X-Forwarded-Port. These headers are typically used when applications operate behind reverse proxies or load balancers that forward the original request context.
In affected versions, these header values were not strictly validated before being used to construct the request origin. Because attackers can manipulate these headers, the application may trust attacker-controlled values when resolving server-side requests.
If the application performs HTTP requests during the rendering process, those requests may be redirected to attacker-specified destinations, allowing attackers to force the server to interact with internal services or external endpoints.
How CVE-2026-27739 Enables SSRF in Angular Server-Side Rendering
The vulnerability originates from Angular SSR’s request origin reconstruction logic, which determines the application’s base URL from incoming request headers. When a request reaches an Angular SSR application, the framework builds the full request origin and uses it when resolving relative URLs and initiating backend HTTP calls during server-side rendering.
In vulnerable versions, Angular SSR trusts several headers when constructing this origin, including:
- Host
- X-Forwarded-Host
- X-Forwarded-Proto
- X-Forwarded-Port
These headers are typically inserted by reverse proxies or load balancers to preserve the original client request information. However, if the application accepts these values without validation, attackers can supply malicious values to influence how the request origin is constructed.
For example, an attacker may modify the X-Forwarded-Host header to specify a domain under their control. When Angular SSR builds the request origin using this value, outbound requests generated during rendering may resolve to that attacker-controlled host. Similarly, manipulating the X-Forwarded-Proto or X-Forwarded-Port headers can alter how URLs are constructed and redirect requests to unexpected destinations.
Exploitation occurs when an attacker sends a request containing manipulated header values such as Host or X-Forwarded-Host. Because Angular SSR relies on these headers to reconstruct the application’s base URL, the attacker can influence how the server interprets the request origin.
During the rendering process, the application may initiate backend HTTP requests using relative URLs. Since the base origin has already been manipulated, these requests resolve to the attacker-controlled host rather than the intended backend service.
As a result, the application server may send requests to destinations specified by the attacker, including:
- Internal APIs
- Private network services
- Cloud metadata endpoints
- Attacker-controlled servers
Because these requests originate from the application server itself, they may bypass network restrictions that would normally prevent external attackers from accessing internal resources.
Potential Impact of SSRF in Angular SSR
If exploited successfully, CVE-2026-27739 can allow attackers to abuse the application server to send unauthorized requests to internal or external systems. Because the requests originate from the server itself, they may bypass network restrictions that normally protect internal services.
- Access to Internal Services – Attackers may force the server to interact with internal APIs, administrative interfaces, or backend microservices that are not directly exposed to the internet. This can help attackers discover internal endpoints and map the application’s internal architecture.
- Sensitive Data Exposure – Internal services may return configuration files, application responses, or other sensitive information. If these responses are relayed back through the application, attackers may retrieve data that was never meant to be publicly accessible.
- Cloud Metadata Access – In cloud-hosted environments, attackers may attempt to reach instance metadata services. These endpoints can contain credentials or configuration details used by the cloud infrastructure.
- Credential Leakage – If the application includes authentication headers, session tokens, or cookies in server-side requests, attackers may capture these credentials by redirecting requests to attacker-controlled endpoints.
The overall impact depends on how the SSR application handles outbound requests and which internal resources are reachable from the application server.
CVE-2026-27739 – Mitigation and Remediation Guidance
Organizations using Angular Server-Side Rendering should take immediate steps to reduce exposure to CVE-2026-27739.
Update Angular Dependencies – The Angular maintainers have released patched versions that address the vulnerability by introducing stricter validation of forwarded headers used during request origin reconstruction. Upgrading to Angular 21.2.0-rc.1, 21.1.5, 20.3.17, or 19.2.21 (or later) is the primary remediation step.
Validate Host and Forwarded Headers – Since the vulnerability is tied to how headers such as Host, X-Forwarded-Host, X-Forwarded-Proto, and X-Forwarded-Port are processed, applications should ensure that these headers are accepted only from trusted proxies and contain expected values.
Avoid Using Request Headers to Build Internal URLs – Applications should avoid constructing internal service URLs directly from client-supplied headers. Instead, backend service endpoints should be defined through trusted configuration or environment variables.
Restrict Outbound Network Access – Limiting the server’s ability to initiate connections to internal networks or sensitive infrastructure endpoints can reduce the potential impact of SSRF attempts.
Monitor Outbound Requests – Security teams should monitor outbound traffic from application servers for unexpected connections to internal IP ranges or unfamiliar external domains, which may indicate attempts to exploit SSRF behavior.
How AppTrana WAAP Helps Mitigate CVE-2026-27739
AppTrana WAAP has provided protection against exploitation attempts targeting CVE-2026-27739 from day zero. By inspecting request headers and identifying abnormal patterns at the application layer, AppTrana prevents attackers from influencing how Angular SSR applications construct request URLs.
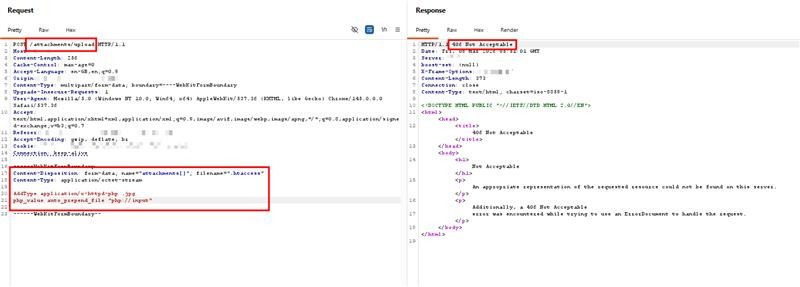
Screenshot showing malicious requests with manipulated headers associated with CVE-2026-27739, detected and blocked by AppTrana WAAP.
Stay tuned for more relevant and interesting security articles. Follow Indusface on Facebook, Twitter, and LinkedIn.