CVE-2026-25639: Axios Vulnerability Triggers DoS in Node.js Applications
A newly disclosed vulnerability tracked as CVE-2026-25639 puts Node.js applications using Axios at risk of remote Denial-of-Service attacks. By sending a specially crafted configuration object, attackers can trigger a fatal runtime error inside Axios’s internal request handling logic, causing the Node.js process to crash instantly.
While Axios is commonly used in both browsers and backend services, the real impact is on server-side environments where an unhandled exception can bring APIs and microservices offline. Given Axios’s widespread adoption across modern Node.js stacks, this vulnerability creates a low-effort path for attackers to repeatedly disrupt production systems.
What is CVE-2026-25639?
Risk Analysis
Severity: High
CVSS v3.x Base Score: 7.5
Attack Vector: CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H
Exploit complexity: Low
Exploit available in public: No confirmed public exploit code
Affected Versions: Axios < 1.13.5
CVE-2026-25639 is a remotely triggerable denial-of-service vulnerability caused by improper handling of crafted configuration objects within Axios. This vulnerability can be exploited over the network without authentication or user interaction, meaning any exposed service that passes attacker-controlled data into Axios configuration logic may be at risk.
Successful exploitation can cause applications to terminate unexpectedly, leading to service disruption, particularly in Node.js environments where unhandled exceptions may crash the entire process.
Technical Root Cause Behind CVE-2026-25639
Axios relies on an internal helper called mergeConfig to combine default settings with request-specific configuration before executing HTTP calls. This function is central to how Axios processes headers, timeouts, adapters, and other runtime options.
CVE-2026-25639 arises when a configuration object contains a crafted __proto__ property. If attacker-controlled JSON input is parsed and passed directly into Axios configuration, the mergeConfig logic does not properly guard against prototype manipulation.
When the function attempts to merge this malformed object, it triggers a TypeError due to unexpected prototype behavior. In Node.js environments, this unhandled exception can bubble up and terminate the process, causing the application to crash.
How CVE-2026-25639 Can Be Exploited
Exploitation of CVE-2026-25639 depends on how an application handles user input before passing it into Axios.
The vulnerability becomes exploitable when:
- An application accepts attacker-controlled JSON data.
- That data is used directly or indirectly as part of an Axios configuration object.
- The supplied object contains a crafted__proto__
When Axios processes this configuration through the mergeConfig function, the malformed prototype structure triggers a runtime TypeError. If the application does not properly catch and handle this exception, the error can propagate and terminate the process.
In practice, this may:
- Crash API endpoints
- Terminate backend services
- Force application restarts
- Disrupt dependent microservices
Because the attack requires no authentication and can be delivered over the network, exposed services that process untrusted configuration data may be susceptible to automated crash attempts.
Operational and Availability Impact of CVE-2026-25639
Axios is one of the most widely used HTTP clients in the JavaScript ecosystem. It is embedded in front-end frameworks, backend services, SDKs, and third-party integrations. As a result, many applications depend on it directly or indirectly.
When a core dependency like Axios contains a vulnerability, the impact can extend beyond a single codebase:
- Multiple applications may inherit exposure through transitive dependencies
- Shared microservices can experience coordinated instability
- API-driven platforms may face repeated service disruption attempts
- Supply-chain risk increases across distributed architectures
Although CVE-2026-25639 does not enable data compromise or remote code execution, targeted crash attempts against production APIs can still lead to downtime, degraded performance, and operational strain.
Availability-focused vulnerabilities in foundational libraries can have broad consequences, especially in high-traffic or enterprise environments where uptime is critical.
Affected Versions
CVE-2026-25639 affects:
- Axios versions up to and including 1.13.4.
The vulnerability is present in earlier releases where the mergeConfig function does not safely handle malformed configuration objects containing crafted prototype properties.
Version 1.13.5 includes the necessary changes to prevent the crash condition triggered by improper prototype handling. Applications running earlier versions remain vulnerable until upgraded to a patched release.
CVE-2026-25639 – Mitigation and Remediation Guidance
The primary remediation for CVE-2026-25639 is to upgrade Axios to version 1.13.5 or later, which resolves the vulnerability. Systems running earlier versions should be updated promptly, particularly where untrusted input may influence request configuration.
In addition to upgrading, organizations should:
- Audit application dependencies to identify both direct and transitive Axios usage
- Avoid passing untrusted or unsanitized JSON objects directly into Axios configuration
- Implement proper error handling to prevent unhandled exceptions from terminating the process
- Use dependency scanning tools within CI/CD pipelines to detect vulnerable package versions
Because Axios is frequently included indirectly through other libraries, teams should verify that patched versions are resolved across the full dependency tree, not just in top-level packages.
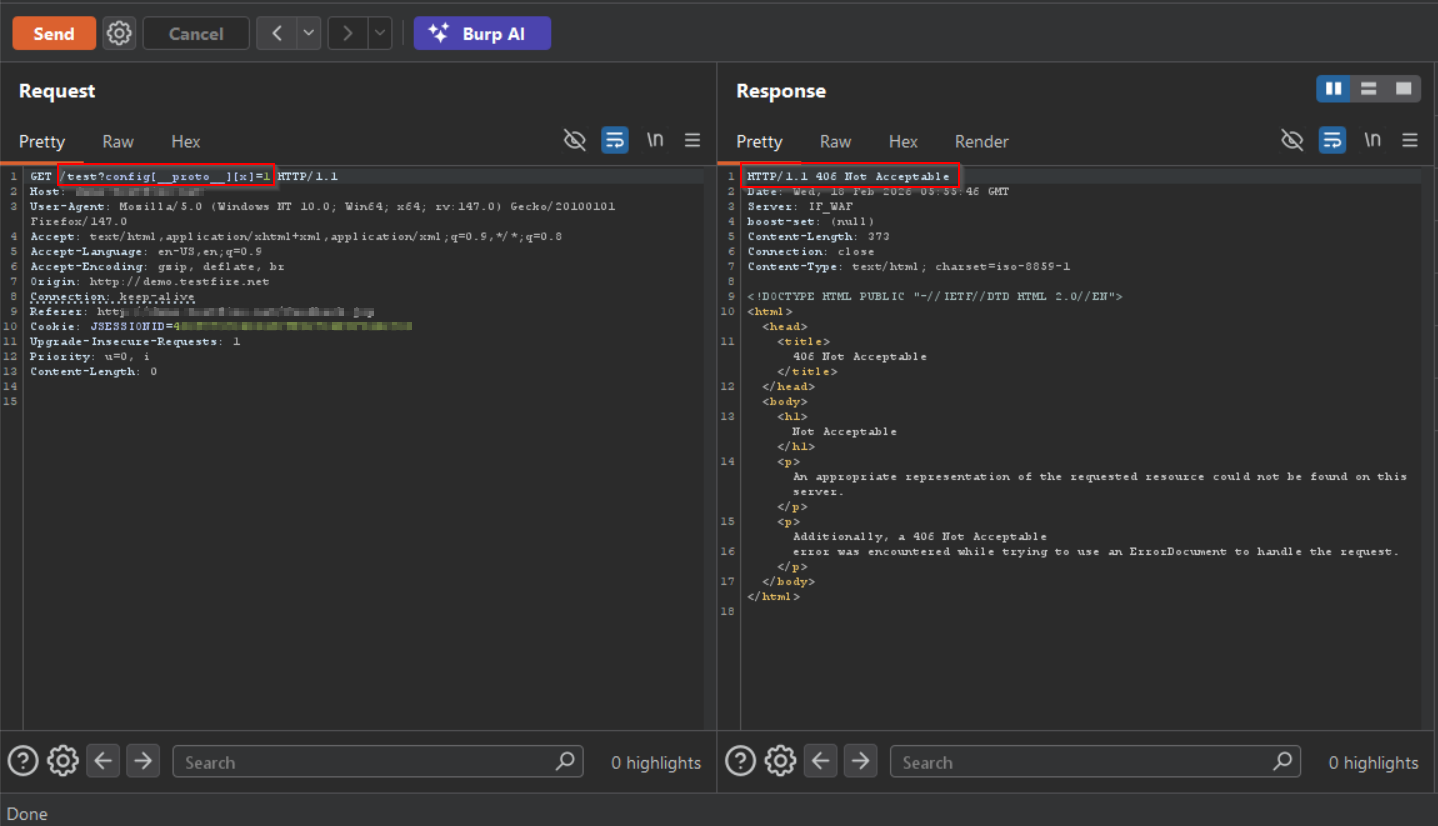
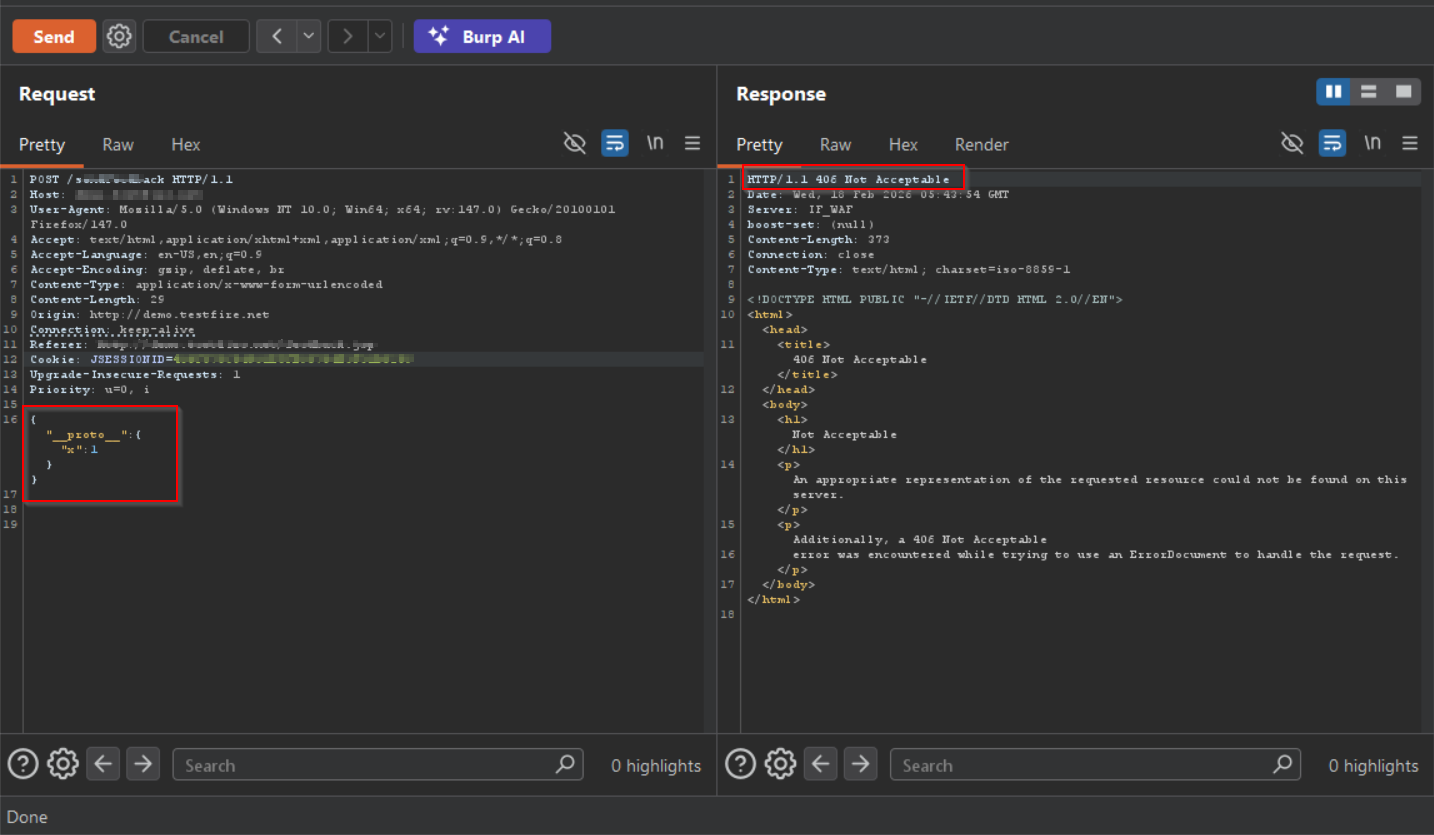
AppTrana WAAP Coverage for CVE-2026-25639
AppTrana WAAP provides immediate protection against exploitation attempts targeting CVE-2026-25639 by blocking prototype pollution payloads at the application layer. Since the vulnerability is triggered through malicious inputs such as __proto__ and related encoded or nested injection techniques, AppTrana’s core WAF protections detect and stop these requests before they reach Axios configuration processing.
By filtering unsafe inputs at the edge, AppTrana helps prevent application crashes and service disruption while teams roll out Axios patches and dependency upgrades.
AppTrana WAAP detecting and blocking prototype pollution payloads linked to CVE-2026-25639.
Stay tuned for more relevant and interesting security articles. Follow Indusface on Facebook, Twitter, and LinkedIn.

 February 24, 2026
February 24, 2026



