Can Penetrating Testing Help Secure Your Business?
Hundreds of thousands of websites and applications are targeted and attacked every day. SANS institute finds that 60% of cyber attacks have targeted web apps. Most web applications have urgent and critical vulnerabilities.
Automatic vulnerability scanners are geared toward evaluating the security posture of the organization. Do you think your automatic scanner alone can cover all aspects of security assessment?
Spoiler alert: No!!!
Automatic tools can only check to a certain point of cyber threats, and nothing can replace the intelligence and expertise of humans.
Hence, it’s in the best interest of every company to prevent cyberattacks through penetration test to uncover possible weaknesses, and address them one by one in a systematic manner.
Why Use a Penetration Test?
A penetration test is intended to simulate a real cyberattack on your network, web applications, systems, and the like. Penetration testing methodology utilizes both manual and automated processes to uncover potential vulnerabilities in your security architecture.
What this means is that with pen testing, you can get a more in-depth understanding of your security systems and their advantages and potential disadvantages.
Where automated security assessment tools may only give you generic “working” or “not working” responses, pen testing will reveal real issues that must be addressed (with additional software, processes, procedures, etc.) if you want to protect your business against possible attacks.
How Does a Penetration Test Work?
These are the main stages a company will go through in a pen test:
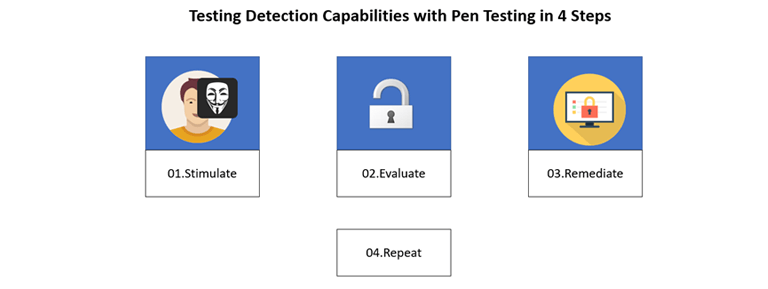
- Planning and Preparation – During this stage, an organization will set goals for their testing efforts, identify testing methods, find security audit partners (if necessary), and the like.
- Testing – Once the planning is complete, it’s time to move forward with the pen test. Tests must be conducted and managed systematically while identifying and investigating vulnerabilities.
- Implementation and Follow Through – Now that weaknesses have been found, it’s time to identify and take action to improve security. Cybersecurity is rarely “set and forget” and will require ongoing maintenance and improvement to be effective over the long term.
Penetration Testing Methodology
There are a variety of penetration testing methodologies that can be employed to uncover a company’s security risk profile. Penetration testing can take many forms depending on the company’s goals and its security infrastructures. In some cases, you may conduct all types of tests for added accuracy.
The main types of penetration testing are as follows:
Internal Testing: This testing simulates an attacker with access to an application behind a firewall. Although this type of scenario could occur due to a malicious insider, an outside attacker could access an employee’s credentials with a phishing attack and proceed to obtain sensitive data, steal trade secrets, make legitimate-sounding payroll requests, and cause other forms of chaos.
External Testing: How secure is your website, web applications, email, or domain name servers? External testing involves hacking into assets that are visible on the web to steal valuable data.
Blind Testing: In a blind test, the only piece of information the tester has is the name of the target company. In this type of testing, your security and/or IT team can observe as a cyberattack is taking place and gather key information about your security structures.
Double Blind Testing: No one at your company will be aware of the simulation as it’s occurring. This means your security team will only be able to respond as they become aware of the attack (just like in a real cyberattack).
Targeted Testing: With targeted testing, the tester and security team will be in direct contact with each other. This can give your security team valuable insights into how a hacker thinks.
Pen Testing to Meet Compliance Standards
At Indusface, clients often come to us to meet their industry-relevant compliance standards. Companies that handle sensitive information often need regular pen testing to attain compliance requirements. Pen-testing report on security posture proves that the mandatory security measures are in place to meet compliance.
GDPR, PCI DSS, ISO 27001, NIST, and CERT-IN are some standards that recommend or require pen testing. It prevents hefty penalties and fines for non-compliance.
Overall, pen testing service providers like Indusface will help you certify for compliance like PCI DSS, CERT-In, and HIPAA and give you the confidence to go through the processes.
Should Every Company Use Penetration Testing in Cyber Security?
With the rapid growth in cybercrime, more than ever, every company must take an interest in its cybersecurity infrastructures.
- Vaadata conducted 200 penetration tests in 2020, and they found that 62% of their clients had medium, important, or critical vulnerabilities in their systems. Your risk tolerance aside, the stats show that most companies aren’t adequately prepared for cyber-attacks.
- If you work in an industry that requires compliance and strict standards and regulations, you should already know just how critical penetration testing is.
- If your company has sensitive data to protect, whether your own or your client’s, then you should also be leaning into preventing cyberattacks through penetration testing.
- Fundamentally, however, every company with networks and web applications should utilize penetration testing to identify and fix holes in their security systems.
Conclusion
A penetration test is a defense against cyber threats because it gives you in-depth insights into your security system. You may deem your assets hacker-proof already, but as the stats show, this is rarely the case.
With cybercrime increasing at an unprecedented rate, regardless of the size of your company, you can’t afford to put off securing your most valuable assets. Use penetration testing to determine the next best steps you can take to improve security.
Stay tuned for more relevant and interesting security articles. Follow Indusface on Facebook, Twitter, and LinkedIn


 September 15, 2022
September 15, 2022



