Unveiling the All-New AppTrana WAAP Dashboard
Discover our new WAAP dashboard: monitor, analyze, and enhance security in real time with visibility and insights to…
Real-time vulnerability analysis, threat intelligence, and expert insights to protect your web, API and AI agents from emerging attacks.
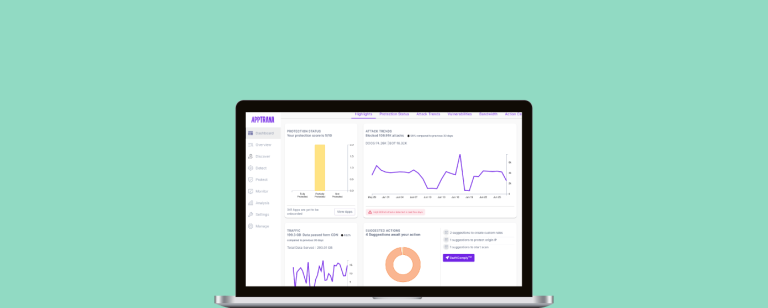
Discover our new WAAP dashboard: monitor, analyze, and enhance security in real time with visibility and insights to…

Indusface is honored in G2’s Best Indian Software Companies 2025 list for Website Security & DAST. See why…

What were the most notorious hacks in history? They’re subject to debate, but we bring you 27 of…
What is Google Armor WAF? Google Cloud Armor is a web application firewall (WAF) service from Google Cloud…

Analyze the pros and cons of AWS WAF and discover the top five alternatives - AppTrana, Akamai, Imperva,…

Akamai vs. Cloudflare WAF compared: Examine pros, cons and unique features of the leading WAF solutions. Learn why…

The Real Breach is in Delay, Not Detection Detecting vulnerabilities is no longer the hard part. With powerful…

Learn how cryptocurrency mining attacks exploit PHP vulnerabilities like CVE-2024-4577, targeting unpatched servers to deploy malicious mining malware.

Penetration testing finds exploitable weaknesses, while vulnerability assessment scans for potential risks. Both are viral for a robust…

Vulnerability management best practices include regular scanning, prioritizing risks, timely patching, continuous monitoring,& adopting a risk-based approach.

Discover how AppTrana WAAP safeguards origin servers from BreakingWAF, a vulnerability exposing 40% of Fortune 1000 firms by…

A critical vulnerability (CVE-2024-9264) in Grafana allows remote code execution, risking system commands and sensitive file access. Immediate…